Cybersecurity news headlines (April 1 – April 15)
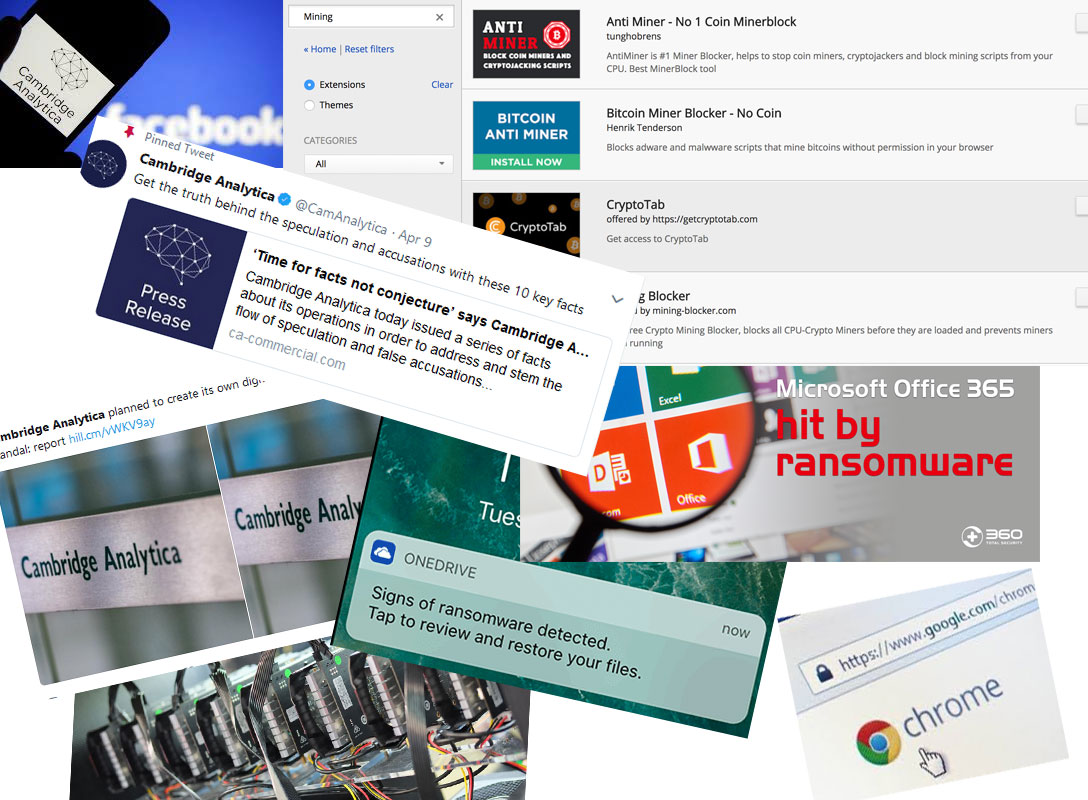
Facebook is still remains in hot waters over the Cambridge Analytica scandal, with more troubling information coming to light. The company revealed that a much larger number of Facebook users had their data access by Cambridge Analytica, an estimated 87 million, instead of the 50 million. It then dropped a bombshell, explaining that by abusing a certain Facebook feature, malicious parties could have gained access to essentially every single Facebook user information. Facebook related news have been dominating the field of cybersecurity, but thankfully, nothing worse has happened in the past few weeks. Below you will find the headlines of April 1 – April 15.
Cambridge Analytica had access to the data of 87 million Facebook users, not 50 million
Back when the Cambridge Analytica scandal first broke out, it was estimated that around 50 million Facebook user data was harvested by the consulting firm. Now, it is estimated that 87 million would be a closer estimation. This information was revealed by Facebook, despite Cambridge Analytica claiming the amount was 30 million instead of 87 million.
“In total, we believe the Facebook information of up to 87 million people — mostly in the US — may have been improperly shared with Cambridge Analytica,” Facebook’s CTO Mike Schroepfer said in a post.
If you didn’t keep track of the whole chain of events, the gist of it is that Cambridge Analytica used an app to harvest the data 87 million Facebook users, Facebook found out and asked the firm to delete the acquired data but failed to check whether the firm actually did that. Which, it allegedly did not. Now Facebook is in hot waters for allowing this to happen and not ensuring their users’ privacy.
Affected users are now being notified with a message on their Facebook timeline. In addition, all users should start seeing messages on their feeds, prompting them to review the apps that have permission to access their Facebook data. If an app was not used for 3 months, Facebook will automatically cut off its access to a user’s data.
In addition to the messages to users, Facebook is also changing how it handles apps. You can find all the implemented changes in the post linked above. One major change is that apps will not longer be allowed to access certain personal information of users.
“We will also no longer allow apps to ask for access to personal information such as religious or political views, relationship status and details, custom friends lists, education and work history, fitness activity, book reading activity, music listening activity, news reading, video watch activity, and games activity.”
Many believe these changes come far too late, however, and Facebook has a lot of work to do in regaining the trust of its users. But users also need to become more concerned about their privacy and regulate the amount of information they share online.
2.2 billion Facebook user data compromised
In another Facebook scandal, the company revealed that most of its 2.2 billion users likely had their personal data accessed by malicious parties. Facebook has (or had) a feature that allows someone to search for a Facebook user by phone number or email address, and reportedly, malicious parties could have used that feature to identify people and gather their profile data. The feature, turned on by default, is optional, and if you are a security cautious user, you will have turned it off years ago. If you haven’t, chances are, someone used it to identify you and access the information you had made public.
CEO Mark Zuckerberg revealed that the feature will be shut down but that is hardly comforting to users. The CEO said the abuse of this feature was detected during a data-privacy audit, which was initiated after the Cambridge Analytica scandal came to light. Zuckerberg also states that the people behind the data scrapping have not been identified.
Users who have set their profiles to private from the very beginning should not be affected by this as only public information was scrapped. But realistically, not many people will have done that.
Microsoft Office 365 built-in ransomware protection
Ransomware has long since become a menace to many users, and despite many warnings to make file backups, many users still find themselves with locked files and no way to get them back. Microsoft Office 365 is now rolling out features that will help home users reduce damages caused by ransomware or other kinds of malware. The company announced new advanced protection capabilities that include file recover in case of an attack, tools to keep information secure, and private and advanced protection from viruses and cybercrime.
Protection against ransomware was already available to Office 365 Business subscribers but the feature is being released for Office 365 Home and Office 365 Personal users as well. The file restore feature will allow users to restore all files in OneDrive to a previous point in time within 30 days. Whether you accidentally deleted files or were attacked by ransomware, you would not need to worry about file loss. When an attack occurs, you will be notified via email, mobile or desktop notification. You would then be guided through the file recovery process.
This feature may help a lot of users save not only money but also prevent the stress that comes with having your files lost or locked by ransomware. However, it still is recommended that all important files are backed up regularly.
Google Bans Chrome Extensions That Mine Cryptocurrencies From the Web Store
In a move to battle cryptojacking, Google has banned extensions mining cryptocurrency from its Web Store. Cryptojacking is becoming a real issues, with a lot extensions providing seemingly useful features while at the same time using user computers to mine for cryptocurrency, unknowingly to the user. Before this change in rules, Google allowed miners to be hosted on their platform, provided that mining is the sole purpose of the extension, and only if the user is fully aware of it. However, according to Google, around 90% of extensions with mining scripts failed to comply to these policies.
“Over the past few months, there has been a rise in malicious extensions that appear to provide useful functionality on the surface, while embedding hidden cryptocurrency mining scripts that run in the background without the user’s consent. These mining scripts often consume significant CPU resources, and can severely impact system performance and power consumption,” it said on the Chromium Blog.
While this is a commendable move, it will not solve the problem completely because malicious extension creators are notoriously good at bypassing Google’s security regulations. An extension could disable the mining function until Google allows the extension to be hosted on the Web Store, and once it has passed all the checks, turn on the mining feature.
Site Disclaimer
WiperSoft.com is not sponsored, affiliated, linked to or owned by malware developers or distributors that are referred to in this article. The article does NOT endorse or promote malicious programs. The intention behind it is to present useful information that will help users to detect and eliminate malware from their computer by using WiperSoft and/or the manual removal guide.
The article should only be used for educational purposes. If you follow the instructions provided in the article, you agree to be bound by this disclaimer. We do not guarantee that the article will aid you in completely removing the malware from your PC. Malicious programs are constantly developing, which is why it is not always easy or possible to clean the computer by using only the manual removal guide.
