Cybersecurity news headlines for April 2022
In April’s edition of cybersecurity news headlines, we discuss 4 major stories. First off, German law enforcement has taken down the world’s largest darknet marketplace Hydra after getting a tip its infrastructure may be hosted in Germany. We also discuss the Russian hacker group Sandworm attempting to target Ukraine’s critical infrastructure, and T-Mobile disclosing that hacker group Lapsus$ was able to breach internal systems. And finally, the US Department of the Treasury has attributed the massive $600 million theft from Ronin network to the North Korean hacker group Lazarus.
Without further ado, here are the stories that made the biggest headlines in April 2022.
The world’s largest darknet marketplace Hydra taken down by German law enforcement
German police have seized a dark web marketplace, Hydra Market, taking down one of the world’s largest darknet marketplaces. With an estimated $1.35 billion turnover in 2020, Russian language Hydra Market sold all kinds of illegal goods, including drugs, stolen credit card information, and fake documents. The marketplace primarily served to provide illegal goods to Russia and its neighboring countries. At the time of the takedown, the dark web marketplace had 17 million registered customers. It was also the longest-running dark web marketplace, having operated since 2015.
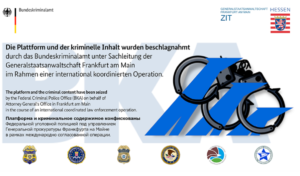
Germany’s Federal Criminal Police Office (BKA) has been investigating Hydra Market since August 2021 when it received information that the marketplace’s infrastructure may be hosted in Germany. Several US authorities were also involved in the investigation. Sebastian Zwiebel, the spokesperson for Germany’s Central Office for Combating Cybercrime (ZIT), told BBC that the investigation began when the agency received a tip-off from US officials. However, locating which firm was hosting Hydra in Germany took months. Once the hosting service was identified, the BKA was able to issue a takedown notice.
But while Hydra Market is no longer operational and visitors are greeted with a police notice saying “the platform and the criminal content has been seized”, its operators have not been apprehended.
“We know they will find another way to do their business. They will probably try to build a new platform, and we will have to keep our eye on it. We don’t know the perpetrators, so that’s the next step,” Zwiebel told BBC.
Authorities have seized over $25 million worth of Bitcoins. It’s also been noted that Hydra Marketplace was involved in cryptocurrency laundering. Marketplace customers/sellers were able to purchase cryptocurrency from others in exchange for rubles and receive cash via payment apps. Alternatively, customers could have opted for a delivery method that involved sellers concealing the cash in a specific location for customers to pick up.
The US Department of the Treasury (USDT) also announced sanctions against Hydra, as well as a Russian cryptocurrency exchange platform Garantex.
“Treasury is committed to taking action against actors that, like Hydra and Garantex, willfully disregard anti-money laundering and countering the financing of terrorism (AML/CFT) obligations and allow their systems to be abused by illicit actors,” the USDT said in a press release.
Sandworm hacker group fails to take down Ukrainian energy provider
Notorious Russian hacker group Sandworm attempted to target Ukraine’s energy provider, five years after successfully carrying out a cyberattack on Ukraine’s power grid. Hacker group Sandworm, also known as Unit 74455, is an alleged Russian cyber military unit. Numerous high-scale cyberattacks are attributed to Sandworm, including the 2015 attack on Ukraine’s power grid, as well 2017 NotPetya attacks on Ukraine.
According to a cybersecurity company ESET, which helped CERT-UA (Computer Emergency Response Team of Ukraine) stop the attack, a new version of the Industroyer malware was used to target the energy provider. The Industroyer malware was used in a previous attack on Ukraine’s power grid. The cyberattack targeting Ukraine’s energy provider was set for April 8 but was prevented by CERT-UA and ESET. During the attack, Sandworm hackers attempted to deploy the new Industroyer malware (dubbed Industroyer2) against high-voltage electrical substations in Ukraine. According to ESET, it’s not currently known how attackers were able to compromise the initial victim or how they were able to move from the IT network to the Industrial Control System (ICS) system.
In addition to the Industroyer2, Sandworm hackers also deployed a new version of the CaddyWiper malware. The malware was likely deployed to slow down the recovery process and prevent the targeted energy company from regaining control of the affected systems.
A cyberattack targeting Ukraine’s critical infrastructure is not unexpected considering the ongoing Russian invasion of Ukraine. Similar attacks will likely occur in the future as well.
T-Mobile’s internal systems breached by Lapsus$
Mobile telecommunications company T-Mobile has confirmed that notorious cybercrime gang Lapsus$ breached its network using stolen credentials and was able to gain access to internal systems. T-Mobile has assured that no customer or government information was accessed during the incident.
Lapsus$ hackers were able to access T-Mobile’s network by compromising employee accounts. Doing this gave Lapsus$ hackers access to T-Mobile’s internal tools, such as Atlas, which is used to manage customer accounts. Reportedly, hackers tried to use their access to Atlas to find T-Mobile accounts associated with the FBI and US Department of Defense. They were unable to successfully access any of the targeted accounts as additional checks are necessary to access them. It’s not certain how attackers were able to compromise employee accounts, but most likely, attackers either carried out a successful social engineering attack themselves or purchased leaked credentials from other cybercriminals. According to cybersecurity specialist Brian Krebs, who had access to messages between Lapsus$ members, when the attackers were cut off from an employee’s account, they would just buy another set of credentials.
While they were not successful in accessing sensitive high-profile accounts, Lapsus$ hackers could have carried out SIM-swap accounts using the employee account access. SIM-swapping attacks involve cybercriminals transferring a phone number to a device under their control. This would allow them to intercept phone calls and messages, including two-factor authentication codes sent via SMS.
“Several weeks ago, our monitoring tools detected a bad actor using stolen credentials to access internal systems that house operational tools software. The systems accessed contained no customer or government information or other similarly sensitive information, and we have no evidence that the intruder was able to obtain anything of value. Our systems and processes worked as designed, the intrusion was rapidly shut down and closed off, and the compromised credentials used were rendered obsolete,” T-Mobile’s statement reads.
However, according to Krebs, Lapsus$ hackers were able to steal source codes for some company projects. Lapsus$ is known for its attempts to extort money from its victims by threatening to publish data if a payment is not made. However, in March 2022, the City of London Police made seven arrests in connection to Lapsus$. The ages of those arrested range between 16 and 21 years old. One of the most prominent Lapsus$ members “White” was also among those arrested.
North Korean hacker group Lazarus linked to $600 million Axie Infinity theft
The notorious North Korean hacker group has been linked to a $600 million cybertheft that happened last month. On March 23, it was disclosed that more than $600 million worth of cryptocurrency was stolen from Ronin, a blockchain network tied to a popular online game Axie Infinity. This is considered to be one of the largest cryptocurrency heists in history.
According to Ronin, the attackers used stolen private keys to steal some 173,600 ether tokens and 25.5 million USD Coin tokens (worth $540 million at the time of the attack). For over a month, no cybercrime group or individual was assigned blame for the attack but the US Department of the Treasury sanctioned a digital currency address used by the hackers as belonging to the North Korean hacking group Lazarus.
Lazarus group is believed to be behind some of the biggest cybersecurity incidents, including the 2014 Sony Pictures Entertainment hack, as well as the massive WannaCry ransomware attack. The US Federal Bureau of Investigation classified the Lazarus group as a state-sponsored hacking organization with strong links to North Korea.
“We are still in the process of adding additional security measures before redeploying the Ronin Bridge to mitigate future risk. Expect the bridge to be deployed by end of month. Security comes first. The timeline is subject to change based on the implementation time of several security measures,” Ronin said in a blog post.
References
- Joe Tidy. Hydra: How German police dismantled Russian darknet site. BBC News.
- Illegaler Darknet-Marktplatz „Hydra Market“ abgeschaltet. Bundeskriminalamt.
- Treasury Sanctions Russia-Based Hydra, World’s Largest Darknet Market, and Ransomware-Enabling Virtual Currency Exchange Garantex. The US Department of the Treasury.
- Industroyer2: Industroyer reloaded. ESET.
- Кібератака групи Sandworm (UAC-0082) на об’єкти енергетики України з використанням шкідливих програм INDUSTROYER2 та CADDYWIPER (CERT-UA#4435). CERT-UA.
- Brian Krebs. Leaked Chats Show LAPSUS$ Stole T-Mobile Source Code. KrebsonSecurity.
Site Disclaimer
WiperSoft.com is not sponsored, affiliated, linked to or owned by malware developers or distributors that are referred to in this article. The article does NOT endorse or promote malicious programs. The intention behind it is to present useful information that will help users to detect and eliminate malware from their computer by using WiperSoft and/or the manual removal guide.
The article should only be used for educational purposes. If you follow the instructions provided in the article, you agree to be bound by this disclaimer. We do not guarantee that the article will aid you in completely removing the malware from your PC. Malicious programs are constantly developing, which is why it is not always easy or possible to clean the computer by using only the manual removal guide.