Emotet is back and is now dropping QakBot banking trojan
After more than five months of inactivity, the Emotet botnet is back in action and is now distributing the QakBot (QBot) banking trojan. Emotet is known as one of the most notorious and most active cyber crime operations. Emotet first emerged in 2014 as a banking trojan that targeted banking credentials but has since evolved into a botnet that allows operators to drop additional payloads onto infected computers. Over the years it has become on the most widespread cyber security threats. It is often used to spread banking trojans but it is also offered as Malware-as-a-Service (MaaS). Ransomware gangs, particularly the Ryuk group, often buy access to the infected computers in order to spread their malware.
Emotet drops QakBot banking trojan
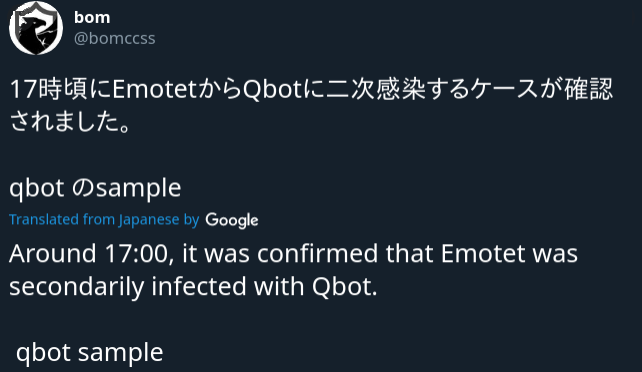
Before it went on a five-month break, TrickBot banking trojan was the malware of choice pushed on infected computers by Emotet. However, not counting the first day after it become active again, it is now spreading the QakBot trojan. The trojan is distributed all across Emotet botnet, through all three of Emotet’s epochs, which are subgroups with their own infrastructure.
“Emotet resurfaced in a massive campaign today after being quiet for several months. The new campaign sports longtime Emotet tactics: emails carrying links or documents with highly obfuscated malicious macros that run a PowerShell script to download the payload from 5 download links,” Microsoft Security Intelligence said on Twitter. They further added that they have noticed several hundred unique attachments and links in tens of thousands of emails in this current campaign.
It has been reported that since its return, 250,000 emails carrying malware have been sent on a daily basis. The emails either contain an attachment or a URL. The emails themselves are pretty standard and disguise the malware as an invoice or some kind of important document. They’re also often sent as replies to existing email threads, a trick commonly used by Emotet. When a user downloads the malware and tries to open it, they are asked to enable macros as they are disabled by default. If a computer is secured with anti-malware software that protects against Emotet, when a user tries to enable the macros they will get a notification that the threat has been blocked, preventing the payload from successfully executing. However, if the threat is not stopped and the macros are enabled, Windows Management Instrumentation launches a PowerShell to retrieve the Emotet binary from one the compromised WordPress sites. A confirmation will be sent to Emotet’s command and control server once the payload has been executed. If someone buys access to computers part of the Emotet botnet, additional malware is downloaded some time after initial infection. Currently, it seems to be dropping the QakBot banking trojan. The QakBot is a banking trojan that spies on users banking activity for a chance to steal large sums of money, often targeting businesses.
It is not clear why Emotet switched from TrickBot to QakBot but it is unlikely to be a permanent change, as it has happened in the past as well. All three, TrickBot, QakBot and Emotet, are part of the same community, thus are convenient partners. It’s also not the first time Emotet went on a hiatus, as it become inactive for a couple of months in 2019 as well.
A large portion of Emotet operations disrupted by an unknown hacker
A couple of days after the Emotet botnet started its operations again, a unidentified hacker started disrupting Emotet’s spam campaign by replacing Emotet’s payloads with GIFs, preventing an infection.
We mentioned above that when users open the file and enable macros, the payload is downloaded from a compromised WordPress website. The compromised sites are managed by Emotet operators via web shells. Those web shells are essentially malware that are installed on hacked servers, which allow attackers to control the servers. It appears that Emotet does not have the best security as a hacker was likely able to guess a password for a web shell and is now replacing the malware payload on the hacked WordPress websites with animated GIFs.
It appears that this has caused a significant disruption in Emotet’s day-to-day operations. According to Kevin Beaumont, a threat intelligence analyst at Microsoft, a quarter of malware is being replaced with GIFs. That would mean significant losses for Emotet.
Who exactly is doing this is not known, though it is speculated that it may be a rival cyber crime gang or a hacker working for the cybersecurity industry trying to halt Emotet’s operations. It may also be Emotet operators themselves, though their motivations for disrupting their own operations would be difficult to guess.
Site Disclaimer
WiperSoft.com is not sponsored, affiliated, linked to or owned by malware developers or distributors that are referred to in this article. The article does NOT endorse or promote malicious programs. The intention behind it is to present useful information that will help users to detect and eliminate malware from their computer by using WiperSoft and/or the manual removal guide.
The article should only be used for educational purposes. If you follow the instructions provided in the article, you agree to be bound by this disclaimer. We do not guarantee that the article will aid you in completely removing the malware from your PC. Malicious programs are constantly developing, which is why it is not always easy or possible to clean the computer by using only the manual removal guide.
