Google warns North Korean hackers are targeting security researchers via social media
Google has warned about a new campaign that is targeting security researchers. Attackers, who Google’s Threat Analysis Group believes to be a “government-backed entity based in North Korea”, are using a number of means to target the security research community.
Google’s Threat Analysis Group (TAG) revealed in a blog post that government-backed North Korean hackers are targeting security researchers working on vulnerability research and development at different companies/organizations via social media. Google has warned the community to “remain vigilant when engaging with individuals they have not previously interacted with”.
According to TAG, the malicious actors create social media profiles and research blogs to establish a connection with security researchers. To appear more credible, they would publish blog posts, videos, etc., on social media like Twitter. The blog posts would contain information about supposed exploits and vulnerabilities in order to build credibility with security researchers. The blog posts don’t always contain accurate information, however. In one instance, a video posted on YouTube on January 14, 2021, and later tweeted on Twitter, shows the malicious actors exploiting a recently patched Windows Defender vulnerability (CVE-2021-1647), but the exploit turned out to fake. The fake exploit video was retweeted by other Twitter accounts created by the same malicious actors.
“Multiple comments on YouTube identified that the video was faked and that there was not a working exploit demonstrated. After these comments were made, the actors used a second Twitter account (that they control) to retweet the original post and claim that it was “not a fake video”,” Adam Weidemann, a security researcher from Google’s TAG said in the blog post.
TAG reports that the malicious actors are targeting specific security researchers. They would first establish initial communication, after which they would invite the researcher to collaborate on vulnerability research and provide a Visual Studio Project. Twitter, LinkedIn, Telegram, Discord, Keybase and email were the platforms used to communicate with the researchers.
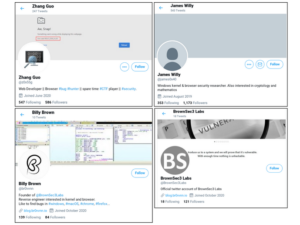 Twitter accounts controlled by the malicious actors (Source: Google)
Twitter accounts controlled by the malicious actors (Source: Google)
“Within the Visual Studio Project would be source code for exploiting the vulnerability, as well as an additional DLL that would be executed through Visual Studio Build Events. The DLL is custom malware that would immediately begin communicating with actor-controlled C2 domains,” the blog post explains.
TAG also notes that social engineering is not the only way malicious actors are targeting security researchers. In certain cases, researchers were compromised after visiting the blog that belongs to said actors. The researchers have reportedly clicked on a link to the blog posted in a tweet, which led to a malicious service being installed on the researchers’ systems shortly after. Google it yet to confirm how the compromise happened exactly, as victims’ systems were running fully patched and updated Windows 10 and Chrome browsers.
The blog post contains a list of known social media accounts controlled by the malicious actors, and Google encourages users to contact TAG if they have information.
Security researchers are likely targeted to acquire information about yet to be disclosed vulnerabilities they have discovered in order to use them for future cyber attacks.
Hey folks, story time. A guy going by the name James Willy approached me about help with a 0-day. After providing a writeup on root cause analysis I realized the visual studio project he gave me was backdoored.
– Alejandro Caceres (@_hyp3ri0n) January 26, 2021
Keep your wits about you. I can confirm I was targeted by “z0x55g” via Twitter DMs asking about browser and Windows kernel 0day vulnerability research. I guess it was because I had commented about the Defender RCE and used to have #0day in my bio. But yikes! Stay vigilant
– Will | Bushido (@BushidoToken) January 26, 2021
WARNING! I can confirm this is true and I got hit by @z0x55g who sent me a Windows kernel PoC trigger. The vulnerability was real and complex to trigger. Fortunately I only ran it in VM.. in the end the VMDK I was using was actually corrupted and non-bootable, so it self-imploded
– Richard Johnson (@richieseattle) January 26, 2021
“We recommend that you compartmentalize your research activities using separate physical or virtual machines for general web browsing, interacting with others in the research community, accepting files from third parties and your own security research,” Google has advised researchers who are concerned about being targeted.
Site Disclaimer
WiperSoft.com is not sponsored, affiliated, linked to or owned by malware developers or distributors that are referred to in this article. The article does NOT endorse or promote malicious programs. The intention behind it is to present useful information that will help users to detect and eliminate malware from their computer by using WiperSoft and/or the manual removal guide.
The article should only be used for educational purposes. If you follow the instructions provided in the article, you agree to be bound by this disclaimer. We do not guarantee that the article will aid you in completely removing the malware from your PC. Malicious programs are constantly developing, which is why it is not always easy or possible to clean the computer by using only the manual removal guide.

