Ransomware Trends to Watch in 2020
Ransomware in 2020
Ransomware has come a long way from the days when it was merely scareware trying to extort money from vulnerable users by claiming they have done something illegal. Over the years it has evolved into a sophisticated threat that causes billions of dollars in damages every year. It now involves sophisticated infiltration and attack techniques, and can cause disastrous consequences.

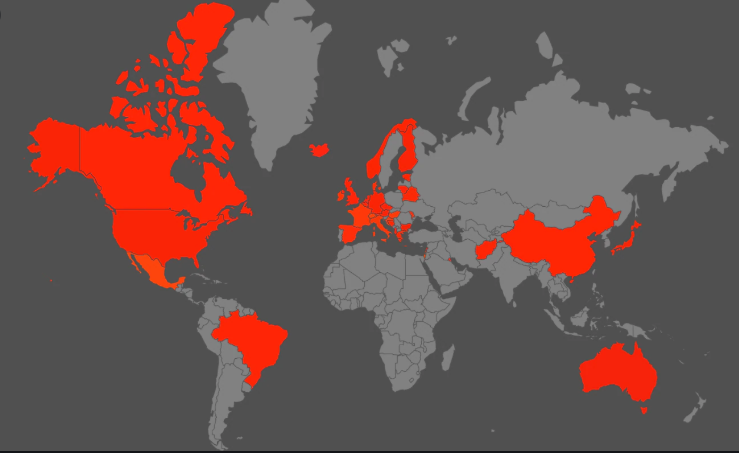
In recent years ransomware has shifted targets, from targeting users randomly to carefully selected individuals, companies, organizations and governments. Healthcare organizations and local governments have become particularly liked targets, with 764 attacks on healthcare, and 113 on state/municipal governments and agencies in just 2019 alone, according to Emsisoft. This has continued on in the first half of 2020, even when the world is battling the COVID-19 pandemic. Some ransomware has also changed its strategy and no longer merely threaten to publicly release data if ransom is not paid, they actually do it. Infections methods are also changing with some ransomware operators opting to buy access to already infected computers and servers instead of doing the infiltration themselves.
Ransomware is ever-changing, and even if cybersecurity is constantly evolving, cyber crooks are always not far behind.
Ransomware attacks shift to specific targets rather than random users
Before, ransomware aimed to spread as widely as possible and targets were mostly regular people. However, targets have shifted over the years, with many ransomware gangs now focusing on specific targets, such as healthcare organizations, smaller businesses and local governments. That is not to say that widespread ransomware campaigns aren’t still happening. They are, but less and less users agree to pay the ransom. Whether out of experience or simply heeding advice, many users have developed a habit of backing up files regularly. If users have backup to their files, there is no need for them to pay the ransom. This means ransomware operators make less and less money, which is why they have shifted their focus to much larger targets.
Local governments are rather common targets now because that is where the big money is. A ransomware infection isn’t just a couple of encrypted files that could be restored from backup quickly, an infection means entire systems could go down. While in operational downtime, government offices are unable to provide everyday services to their citizens and suffer serious financial loss. When faced with such an attack, some make the decision to pay the requested ransom, while others try restore everything from backup. Whatever the case may be, an attack has serious consequences.
Riviera Beach, Florida got infected last June and agreed to pay the $600,000 ransom to restore their systems. La Porte County paid $130,000 after the ransomware infected backup servers. Jackson County, Georgia paid $400,000, Lake City, Florida – $500,000. For many local governments, paying the ransom is ultimately cheaper than restoring their systems on their own, but giving into the demands is only inviting more attacks.
Smaller businesses and healthcare organizations are also convenient targets because they often have lax security and are not prepared to deal with such attacks.
Ransomware attacks target healthcare
In recent years, healthcare organizations have become common targets of ransomware. Not only are they more prone to giving into the demands to pay a ransom but they’re also often not prepared to handle an attack. Because of lax cyber security in many hospitals and other healthcare facilities, cyber crooks are able to easily infect their systems with ransomware. And once an infection has settled in, a lot of organizations do not have proper incident response plans that would allow them to deal with the infection in the most efficient way.

A ransomware attack on a hospital could disrupt regular functions, which impacts how patients are treated. In these situations restoring normal functionality becomes a priority, and paying the ransom can often be the quickest way to do that. However, giving into these demands signals to ransomware operators that they could be targeted again, and ultimately encourages cyber criminals to continue their malicious activity.
This trend of attacking healthcare organizations is not going away any time soon. But as such attacks become the new normal, organizations will implement better security to protect themselves and create incident response plans that will efficiently recover systems without paying the ransom.
Attacks on healthcare still occurring, despite the COVID-19 pandemic
The COVID-19 pandemic has put the healthcare industry in complete chaos, with hospitals all over the world struggling to cope with the onslaught of patients. The last thing they need is a cyber attack.
Healthcare organizations have recently become a popular target among ransomware gangs but according to reports, certain ransomware groups have said they will stop attacks for the time being. BleepingComputer reported back in March that some ransomware operators have said they will stop targeting healthcare organizations during the coronavirus pandemic. Multiple ransomware gangs (CLOP ransomware DoppelPaymer ransomware, Maze ransomware, Neflilim ransomware) responded to BleepingComputer’s inquires about attacks during the pandemic and have said healthcare will not be a target. They also claim that if it happened by accident, free decryption tools would be provided. However, even if they were given a decryption tool for free, hospitals would suffer downtime they really cannot afford at this time.
Nevertheless, it appears that some cyber crooks have no intentions to stop targeting healthcare during this crucial time. Ryuk ransomware, one of the most notorious ransomware, has continued with their attacks, according to security researchers. Targeting healthcare organizations and hospitals is bad enough, but doing it when they are already struggling to keep up with the huge numbers of patients could have devastating consequences.
Despite these promises to stop, many threat analysts have reported that ransomware attacks on healthcare are still as common as ever.
Ransomware threaten to release data publicly if ransom is not paid
In addition to changing targets, ransomware are also altering their modus operandi. Some ransomware are not only encrypting files but also threaten to publicly release them if ransom is not paid. This is not a new threat, cyber crooks have threatened to expose information before, but only recently have they started actually doing it. Before, it was only used as a scare tactic to pressure people/companies into paying the ransom. For those dealing with sensitive information, this would be quite an effective extortion technique. However, recently some ransomware have started making good on the threats. The notorious Maze ransomware group actually published some of the data it had stolen, proving that it’s no longer just a threat.
With more and more organizations realizing how much of a threat ransomware actually is, they will likely implement better security and have data recovery options. As a result, less companies will pay the ransom, and to avoid losing such a big money source, many ransomware groups will likely switch to these new tactics as well. The possibility of potential exposure of sensitive information would pressure companies into giving into the demands and paying the ransom.
Ransomware infection methods are also changing
Finally, ransomware is not only evolving in how it operates and who it targets, it’s also using different infection techniques. Spear phishing and insecure Remote Desktop Protocol (RDP) connections are still the most common ways ransomware spreads but malicious actors have also started buying access to already hacked systems. Hackers sell access to hacked computers and servers on online marketplaces.
Malicious actors can also pay for a botnet to deliver their malware onto computers part of the network. Security researchers have noticed that botnet Emotet, trojan TrickBot and ransomware Ryuk seem to be connected. Devices part of the Emotet botnet often get infected with the credential-stealing trojan TrickBot, and later with Ryuk ransomware. This indicates that Ryuk ransomware operators are buying access to already infected systems. This is likely to become an even more common practice in the future.
Site Disclaimer
WiperSoft.com is not sponsored, affiliated, linked to or owned by malware developers or distributors that are referred to in this article. The article does NOT endorse or promote malicious programs. The intention behind it is to present useful information that will help users to detect and eliminate malware from their computer by using WiperSoft and/or the manual removal guide.
The article should only be used for educational purposes. If you follow the instructions provided in the article, you agree to be bound by this disclaimer. We do not guarantee that the article will aid you in completely removing the malware from your PC. Malicious programs are constantly developing, which is why it is not always easy or possible to clean the computer by using only the manual removal guide.
