How to delete Wisz ransomware
Wisz ransomware is malware that encrypts files. It’s another version of the Djvu/STOP ransomware, operated by a notorious group of cyber criminals who release new versions regularly. It’s classified as a very dangerous infection because file recovery is not always possible.
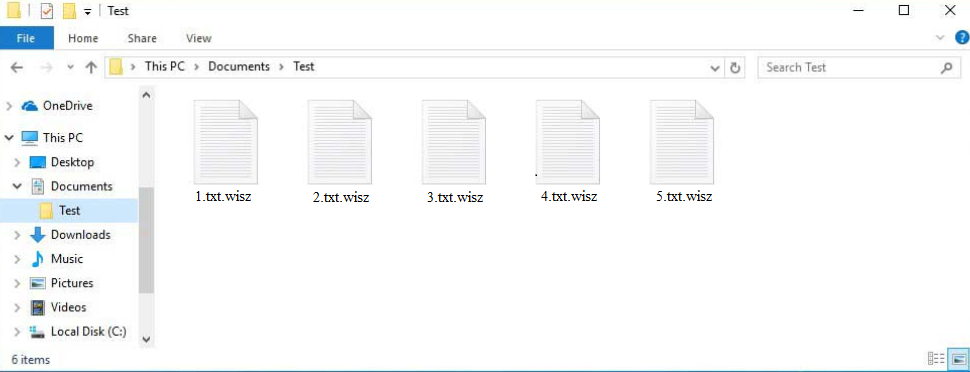
Wisz ransomware encrypts all personal files. It starts the encryption process as soon as the malicious file is initiated. Wisz ransomware will encrypt your photos, videos, documents, etc., essentially all files you’d be most willing to pay for. It’s easy to differentiate encrypted files because they have a .wisz extension added to them. For example, a 1.txt file would become 1.txt.wisz if encrypted. You will not be able to open any of these files unless you first use a decryptor on them.
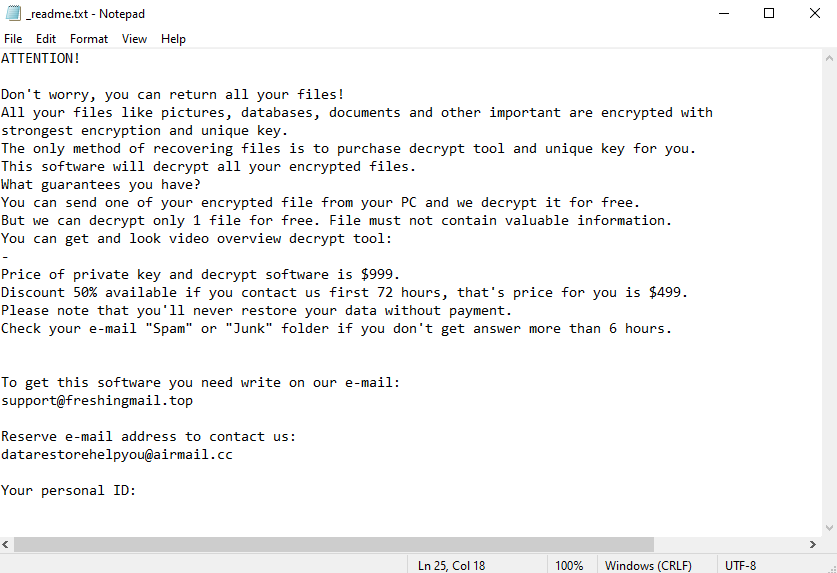
Instructions on how to get the decryptor are provided in the _readme.txt ransom note. The note explains that to get the decryptor, paying a $999 ransom is necessary. Supposedly, users who contact the cybercriminals within the first 72 hours will receive a 50% discount. The note also mentions that users can get one file decrypted for free if it does not contain important information. It’s supposed to be evidence that malware operators have a working decryptor.
Paying the ransom is never recommended for several reasons. Firstly, you will not necessarily get a decryptor just because you pay. Keep in mind that you are dealing with cyber criminals, and there’s nothing to force them to send a decryptor. Unfortunately, many users have not received decryptors in the past despite paying. Furthermore, the money users pay to cybercriminals goes towards future criminal activities.
ATTENTION!
Don’t worry, you can return all your files!
All your files like pictures, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
–
Price of private key and decrypt software is $999.
Discount 50% available if you contact us first 72 hours, that’s price for you is $499.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.To get this software you need write on our e-mail:
support@freshingmail.topReserve e-mail address to contact us:
datarestorehelpyou@airmail.ccYour personal ID:
To remove Wisz ransomware you will need to use a good anti-malware program. Ransomware is a very complex infection and should not be removed manually because you could end up causing more damage to your computer. When you fully delete Wisz ransomware, you can safely access your backup and start recovering files. Your file recovery options are limited if you do not have a backup. The only option is to back up the encrypted files and wait for a free Wisz ransomware decryptor to be released. However, free decryptors are not always released, so a free Wisz ransomware decryptor is not guaranteed.
How is ransomware distributed?
Users can pick up ransomware in several different ways, and it’s usually because they have bad browsing habits and engage in risky behavior. If users open unsolicited email attachments or use torrents to pirate copyrighted content, they’re much more likely to pick up an infection than those who have good online habits. Developing better habits as well as becoming familiar with common malware distribution methods is an effective way to avoid malware.
Malware is commonly distributed through email attachments. Users whose email addresses have been leaked in the past are the usual targets of these emails. The emails can be disguised as parcel delivery notifications or order notifications, with senders claiming that important files are attached to emails. When users open these attached files, they allow the malware to initiate. Fortunately, many malicious emails are generic and are not difficult to identify as malicious. One of the most noticeable signs is grammar/spelling mistakes. The senders pretend to be from legitimate companies but when the text is full of grammar/spelling mistakes, it becomes obvious that the email is not legitimate. Another sign is generic words like User, Member, Customer, etc., used to address users. When companies email their customers, they use their names to address them. For example, order confirmation emails contain users’ personal information that they provide when making the order. However, malicious emails target many users at the same time so they use very generic language.
Some malicious emails can be much more sophisticated, especially when the target is someone specific. It’s strongly recommended to scan all unsolicited email attachments with anti-malware software or VirusTotal before opening them.
Malicious actors also use torrents to distribute malware. Torrent sites are often quite poorly moderated, which allows cybercriminals to upload torrents with malware in them. Torrents for entertainment content are most likely to contain malware, especially torrents for movies, TV series, and video games. It’s strongly discouraged to use torrents to pirate copyrighted content because it’s not only content theft but also dangerous for the computer/data.
Wisz ransomware removal
If you have a backup, you should be very careful not to connect to it until you remove Wisz ransomware from the computer. If the ransomware is still present when you access it, the backed-up files will become encrypted as well. To remove Wisz ransomware, using a good anti-malware program is recommended because it’s a complex infection. If you try to delete Wisz ransomware manually, you could end up causing additional damage to your computer. When your anti-malware program no longer detects the ransomware, you can connect to your backup and start recovering files.
If backup is not an option, file recovery is not possible at the moment. Malware researchers are sometimes able to release free decryptors but ransomware versions from the Djvu/STOP malware family are notoriously difficult to crack. Thus, a free Wisz ransomware decryptor is not currently available. If it does get released, you should be able to find it on NoMoreRansom. If it’s not available there, you will not find it anywhere else. You should also keep in mind that there are many fake decryptors advertised on various questionable forums. Downloading a fake decryptor could lead to a serious malware infection.
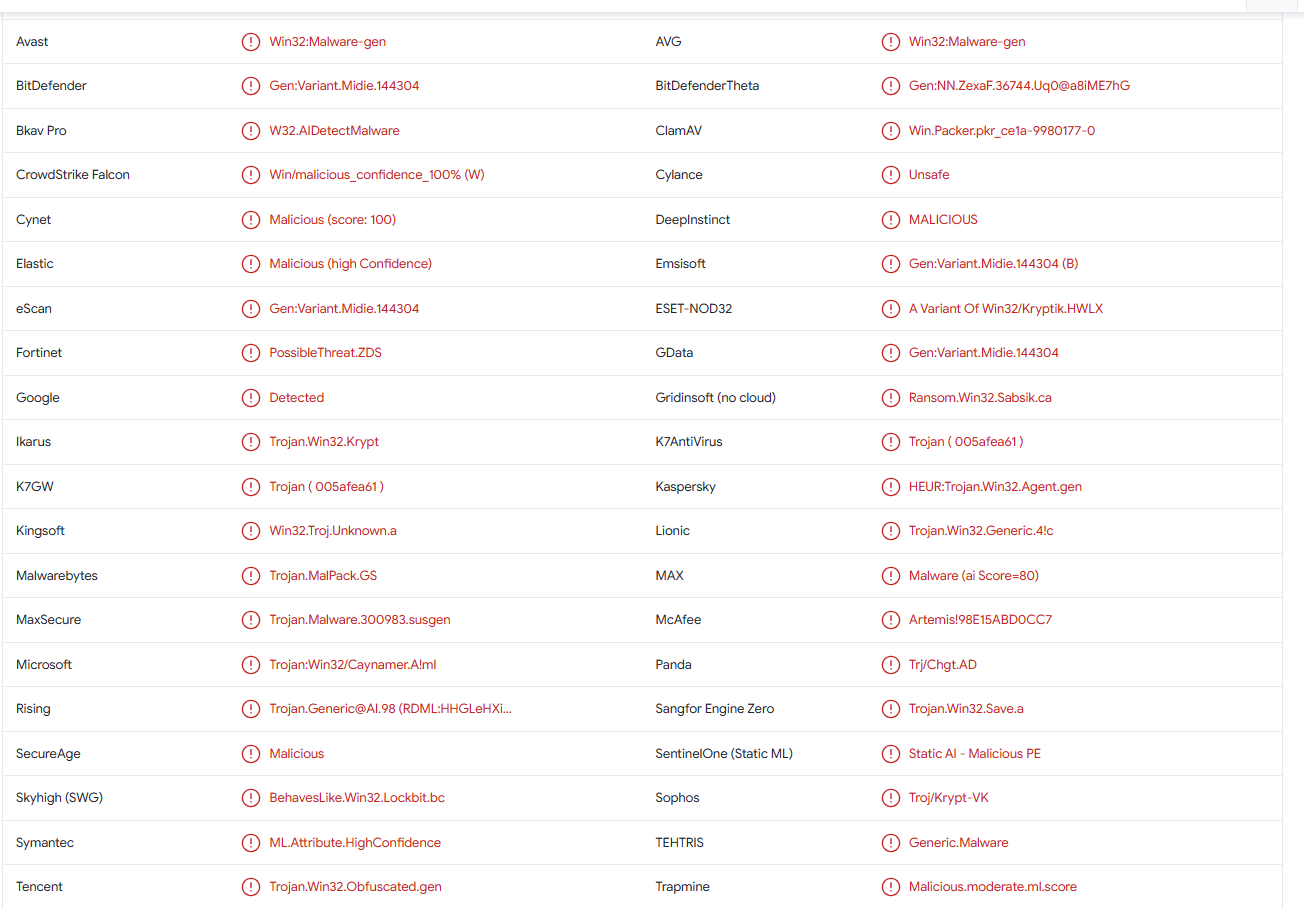
Wisz ransomware is also detected as:
- Win32:PWSX-gen [Trj] by Avast/AVG
- A Variant Of Win32/Kryptik.HWLX by ESET
- HEUR:Trojan.Win32.Agent.gen by Kaspersky
- Gen:Variant.Midie.144304 by BitDefender
- Trojan.MalPack.GS by Malwarebytes
- Trojan:Win32/Vidar.SPXX!MTB by Microsoft
Site Disclaimer
WiperSoft.com is not sponsored, affiliated, linked to or owned by malware developers or distributors that are referred to in this article. The article does NOT endorse or promote malicious programs. The intention behind it is to present useful information that will help users to detect and eliminate malware from their computer by using WiperSoft and/or the manual removal guide.
The article should only be used for educational purposes. If you follow the instructions provided in the article, you agree to be bound by this disclaimer. We do not guarantee that the article will aid you in completely removing the malware from your PC. Malicious programs are constantly developing, which is why it is not always easy or possible to clean the computer by using only the manual removal guide.