How to remove DUCKTAIL trojan
DUCKTAIL trojan is a malicious infection used for targeted attacks against prominent Facebook Business pages. Malicious actors use this malware to hijack Facebook Business/Ads pages and steal sensitive data. It’s a serious infection that can cause a lot of damage.
DUCKTAIL trojan operators use various social engineering techniques to target specific users, and if they successfully trick the user into opening a malicious file, the DUCKTAIL trojan can initiate and begin its malicious activities. The first thing DUCKTAIL trojan does is check whether Google Chrome, Mozilla Firefox, Microsoft Edge, or Brave browsers are installed. If these browsers are installed, the malware looks for specific cookies. The cookies it’s interested in are ones that contain data that would allow the malware access to the target’s Facebook account. DUCKTAIL trojan also checks whether the targetted user’s Facebook account is protected with two-factor authentication (2FA). If 2FA is enabled, the malware will also attempt to steal recovery codes that would allow it to bypass 2FA. If the DUCKTAIL trojan successfully steals this information, it will access the target’s Facebook Business account and add an email address that belongs to the malware operators. Once the email address is added, the attacker gets access to the account.
In particular, people in certain positions are targeted, with the most common targets being those in digital marketing, digital media, and human resources positions. People in these positions may be contacted through social media sites, such as LinkedIn, and tricked into downloading and opening a malicious file on their computers.
Once the malware gains access to a Facebook Business/Ads account, it proceeds to steal information, including linked emails, names, ad spending, account permissions, client data, and connected account numbers.
How does the DUCKTAIL trojan spread?
DUCKTAIL trojan is used to target specific users, so to increase the chances of a successful attack, the malware is distributed via tailor-made attacks. Most commonly, phishing and social engineering are used for attacks.
Targets may be contacted via platforms like LinkedIn. Malicious actors may engage with the targets for some time before sending a malicious file. It can also be found on Dropbox, MediaFile, and iCloud platforms. If opened, malicious files would result in an infection.
DUCKTAIL trojan may also be distributed via email. Since specific people are usually targeted, the emails would be tailor-made and contain information that would give them credibility, thus increasing the chances of users opening them. Sophisticated email attacks can appear very convincing. Thus, it’s very important that users, especially those who manage social media accounts, know how to recognize potentially malicious emails. Security measures should also be put in place to prevent users from opening malicious files.
DUCKTAIL trojan removal
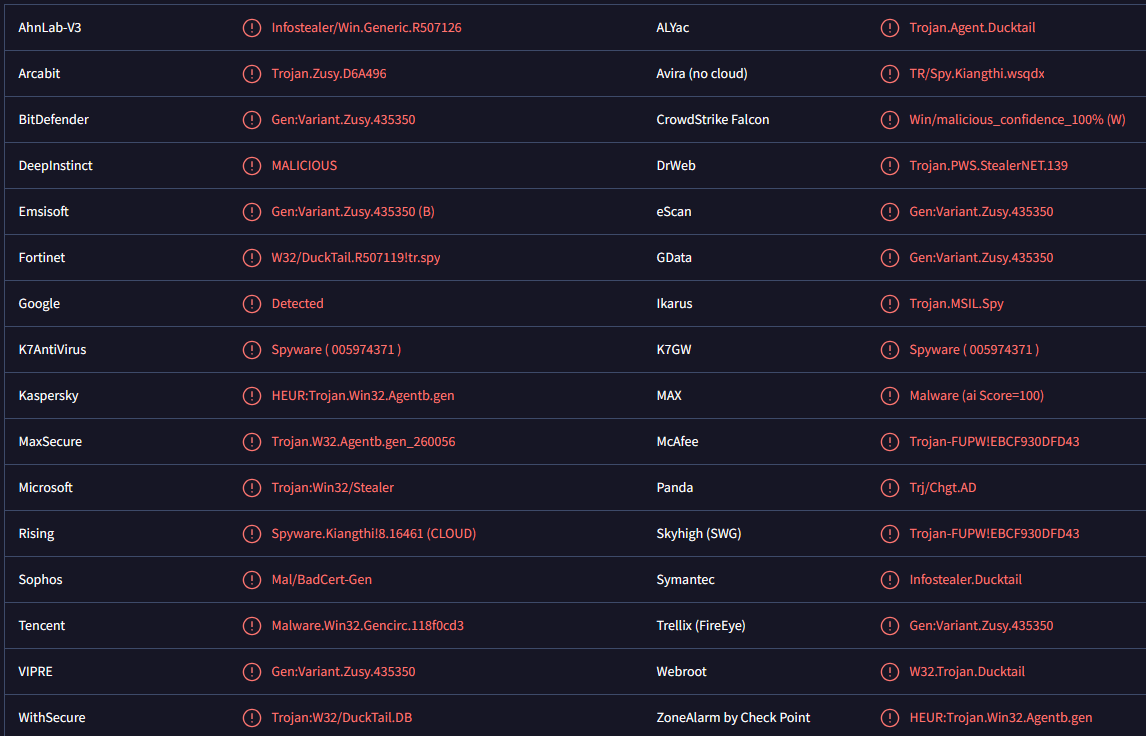
The Trojan would likely go unnoticed without an anti-malware program. This is why having an active security program on a device is so important as it would have prevented the infection from initiating in the first place.
If the DUCKTAIL trojan is detected on a device, users need to immediately remove DUCKTAIL trojan and change all social media and sensitive account passwords to secure accounts. Users’ Facebook and Facebook Business/Ad accounts should also be carefully inspected, and any access by unauthorized devices should be removed.
Site Disclaimer
WiperSoft.com is not sponsored, affiliated, linked to or owned by malware developers or distributors that are referred to in this article. The article does NOT endorse or promote malicious programs. The intention behind it is to present useful information that will help users to detect and eliminate malware from their computer by using WiperSoft and/or the manual removal guide.
The article should only be used for educational purposes. If you follow the instructions provided in the article, you agree to be bound by this disclaimer. We do not guarantee that the article will aid you in completely removing the malware from your PC. Malicious programs are constantly developing, which is why it is not always easy or possible to clean the computer by using only the manual removal guide.