Mobile Malware Evolution 2019 [Part 1]
Android Malware
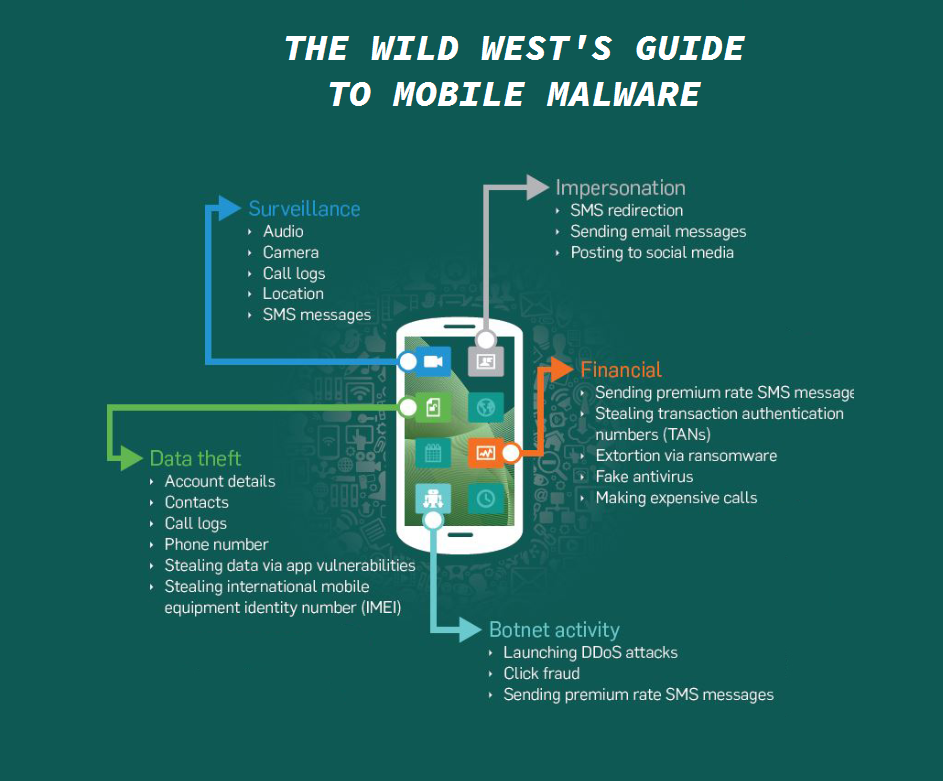
Every smartphone user is essentially carrying around a small computer in their pockets. And because many people keep valuable information on their phones, they’re becoming a target. Malware used to focus on computers in the past, but nowadays, you’re equally likely to have malware on your smartphone. Starting from adware that constantly shows you ads, to ransomware that takes your files for hostage, you can encounter all kinds of threats if you are not careful. They can steal your personal information, phish your online bank logins, spy on your conversations/browsing, bombard your screen with ads, subscribe you to a paid services via SMS, and completely wipe your phone of data.
If you want to have any chance of protecting yourself, you need to become familiar with the types of malware you can encounter. Here is the list of Android malware that you need to be careful of.
Less severe malware for Android
Adware
A threat most commonly encountered by Android users is adware. As the name suggests, it’s a type of infection that aims to expose you to advertisements in order to generate revenue. There are a couple of types of adware you might encounter, one that constantly bombards your screen with ads, and one that engages with ads in the background without you noticing. Adware can disguise itself as a legitimate app, preventing users from quickly getting rid of the infection. In situations when the cause of the ads is not apparent, users have to delete/disable apps one by one in order to find the culprit. It can be quite a time-consuming but necessary process when an anti-virus app fails to detect the issue.
It’s one of the less severe Android infections you can get, but it’s certainly annoying. The one that shows you ads is easily noticeable because ads will pop-up everywhere, sometimes even on the lock screen. While such ads are relatively harmless, interacting with them is not something you should do. Adware is certainly not a reliable source, and a single click could result in a much more serious infection. The constantly popping up ads will also slow down your device and disrupt your regular use.
The other type of adware engages with ads in the background, allowing the infection to make revenue without you having to click on any ads yourself. They are known as ad clickers. The clicker automatically clicks on ads, even when you do not see them. Despite the fact that the ads are not always visible, such adware is easily noticeable, although symptoms are similar to other threats. Because the adware is constantly clicking on ads in the background, you device will suffer the brunt of it. Your battery will run out much more quickly, the device will slow down, and if you’re on a mobile data plan, your data will run out very fast.
Adware also tends to spy on users, collecting information about browsing habits, interests, etc., all so that it can generate more relevant content for you, making it that much more likely that you will click on ad.
SMS subscribers
SMS subscribers are Trojans that subscribe you to paid services without you knowing. They usually come disguised as legitimate apps in order to avoid detection, and send out messages to certain paid services in order to subscribe you to them, or call premium numbers. Those messages are sent without you knowing and they are not visible among your SMS, and phone calls will not be in your call logs.
While not initially noticeable, you will eventually become aware of them because unknown charges will appear in your phone bill. It’s recommended to monitor the phone bill, at least once in a while, to look for unidentified charges. If you do notice one, you should be able to unsubscribe to it via your online account.
Moderately serious Android malware
Mobile cryptocurrency miners
Cryptocurrency became quite popular in recent years, and with that popularity came cryptocurrency mining malware. They were primarily targeting PCs but have since started to infect smartphones as well. Mining malware is not exactly harmful in the sense that it does not delete files or hold them hostage, or steal your personal information, but it’s not harmless.
What cryptocurrency miners do is they use your device’s resources to mine for cryptocurrency. If you have no idea how digital currency mining works, it may all seem confusing. But in very basic words, miners use those resources to solve difficult mathematical equations, solving which is rewarded with the currency that is mined.
Mining consumes enough of the resources to make it very noticeable. One of the first things you will notice is that your Android phone is heating up all the time. That shouldn’t normally happen, and in addition to your phone acting sluggishly and your battery draining quickly, it’s an obvious sign that you are dealing with a miner.
You can end up with a miner in the same ways you would with any other malware. However, they can also disguise themselves as legitimate apps and slip past Google Play’s security. Google has enforced stricter rules recently, so it’s much more difficult for miners to slip past, but it’s still possible. Therefore, even when you’re downloading apps from the official store, you still need to be careful. Research apps, check the permissions and read reviews.
Apart from disrupting your regular computer usage, a miner shouldn’t do damage to your device if it doesn’t stay for a long time. In worst case scenarios, if a miner stays for a long enough time, the constant overheating could actually damage your Android smartphone.
Spyware
As is obvious from the name, spyware is piece of software that primarily spies on you. There are different types of spyware, ones that focus on spying on communication (SMS, email, social media apps, etc.), other that try to steal personal information, files, browser history, locations, and ones that turn on microphone/camera to record conversations/videos.
Spyware generally stays in the background in order to spy on you as long as possible, so you might not necessarily notice it at first. While it may not sound like it at first, spyware is very dangerous, particularly if you store sensitive files on your smartphone.
Some spyware can be manually installed on a victim’s device by ill-intentioned people, such as distrustful partners. This can allow them to track the victims, know their locations, monitor their communications, etc. Not only is that incredibly intrusive behavior, but it’s also illegal in many countries.
Because it doesn’t usually show any obvious signs, an anti-virus app may be the only way to detect spyware.
Keyloggers and banking Trojans
Keyloggers are a piece of software that log your keystrokes. They are more commonly encountered on computers, but also affect smartphones. Everything you type is recorded and sent to cyber crooks, so not only can your passwords be stolen, crooks could gain valuable insight from your parts of SMS and social media app conversations. Keyloggers work in the background so again, without anti-virus you might not notice it.
Banking Trojans are a particularly dangerous type of spyware because they could lead to financial loss. When you try to access your banking app, your typical banking Trojan will replace the actual login page with its own, almost identical page. Without suspecting anything, you would enter your login details, only to provide them to cyber crooks. Such Trojans can also intercept SMS messages sent by your bank, providing crooks information about your accounts.
Continued in part 2 of Android malware.
Site Disclaimer
WiperSoft.com is not sponsored, affiliated, linked to or owned by malware developers or distributors that are referred to in this article. The article does NOT endorse or promote malicious programs. The intention behind it is to present useful information that will help users to detect and eliminate malware from their computer by using WiperSoft and/or the manual removal guide.
The article should only be used for educational purposes. If you follow the instructions provided in the article, you agree to be bound by this disclaimer. We do not guarantee that the article will aid you in completely removing the malware from your PC. Malicious programs are constantly developing, which is why it is not always easy or possible to clean the computer by using only the manual removal guide.
