Remove Zfdv ransomware
Zfdv ransomware is a new Djvu/STOP variant. It’s a very generic ransomware infection, practically identical to most other Djvu versions. It will encrypt your personal files and demand that you pay for their decryption. Encrypted files can be recognized by the .zfdv extension and the fact that you cannot open them. The cybercriminals operating this ransomware will offer you a decryptor if you’re willing to pay almost a thousand dollars for it. But paying the ransom comes with risks that you need to be aware of before making a decision. If you have copies of your files in a backup, you should be able to recover files fairly easily as long as you first remove Zfdv ransomware from your computer. For users without backup, file recovery will be more difficult, if not potentially impossible.
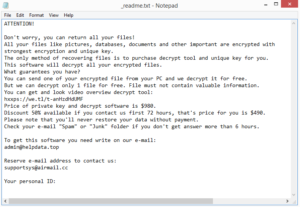
Zfdv ransomware is practically identical to Zpps, Fefg, Fdcv, etc. While some Djvu versions are more widespread than others, they are all equally dangerous. They target personal files and encrypt them. This ransomware will encrypt all of the most common file types. You can expect your photos, images, videos, documents, etc., to be encrypted. Affected files will have .zfdv added to them. For example, image.jpg would become image.jpg.zfdv. When file encryption is done, the ransomware will drop a _readme.txt ransom note. The note explains how you can get the decryptor. Unfortunately, it involves paying $980. The note also mentions a 50% discount for users who make contact with cybercriminals within the first 72 hours, but whether the promise is real is debatable. In general, paying the ransom and buying the decryptor is risky. The decision is yours, but keep in mind that you are not guaranteed a Zfdv ransomware decryptor. Cybercriminals do not operate their ransomware like a regular business, no matter how much they like to pretend otherwise. There’s nothing to guarantee that they will keep their end of the deal if you pay the ransom. In fact, many ransomware victims have failed to receive their decryptors despite paying hundreds of dollars. Furthermore, your money would go towards future criminal activities. But again, whether to pay or not is your decision to make.
You can start recovering your files from backup as soon as you remove Zfdv ransomware from your computer. Make sure to use a reliable anti-malware program because ransomware is a very complex infection. When the ransomware is completely gone, you can safely access your backup.
File recovery will be more difficult, if not impossible if you do not have a backup. You do have the option of waiting for a free Zfdv ransomware decryptor to become available but whether it will even be released is not certain. The thing about ransomware from this family is that they use online keys to encrypt files. This means that the keys are unique to each victim. You would need your individual key for a decryptor to work on your files. So unless those keys are released by the cybercriminals, a free Zfdv ransomware decryptor is not necessarily possible. It’s not impossible that the keys will eventually be released but it may take a while. So while you wait, back up your encrypted files and store them safely until then.
How does ransomware infect computers?
Ransomware, like most malware, is distributed via email attachments, torrents, malicious ads, etc. It’s generally users who have bad online habits that infect their computers with malicious software, which is why it’s so important to develop good browsing habits. We also recommend taking the time to familiarize yourself with the most common malware distribution methods.
You always need to be very careful with email attachments, particularly from unknown senders. Something as simple as opening an email attachment could result in a computer being infected with something malicious. But emails carrying malicious attachments are generally quite obvious. Maybe it’s because the ransomware operators are not proficient in the English language or maybe they just do not care enough to put the effort into their spam campaigns, but the emails are often full of grammar/spelling mistakes. When the sender claims to be from a known company but their email looks unprofessional because of the mistakes, it’s a rather big red flag. Another obvious sign of a potentially malicious email is the way you are addressed. Emails whose attachments you should open will address you by name. Companies of which you are a customer will automatically insert your name into any correspondence they send you. For example, if you use Netflix, notice how all of its emails address you by the main profile name. When a seemingly important email addresses you with generic words like Customer, Member, User, etc., you should be suspicious. At least suspicious enough to not immediately open the attached file. It bears mentioning that there are much more sophisticated malware campaigns, ones that can be incredibly convincing and trick even the most cautious user. This is why it’s a good idea to scan all email attachments with anti-virus software or VirusTotal before opening them.
Torrents are also a common way users pick up malware. Torrent sites aren’t known for their great security, and uploading torrents with malware in them is not difficult. In fact, malicious actors often try to trick users by adding malware to torrents for popular movies, TV series, software, video games, etc. Not only is torrenting copyrighted content essentially stealing, but it’s also dangerous for the computer and your data.
Zfdv ransomware removal
It’s strongly recommended to use anti-malware software to delete Zfdv ransomware from the computer. This is a complex infection that should be dealt with by professional software. If you try to remove Zfdv ransomware manually but have little knowledge about what to do, you could end up causing additional damage to your computer. Furthermore, removing all ransomware components is essential, and missing something could allow the ransomware to recover. If that were to happen while you were recovering files from your backup, those backed-up files would become encrypted as well. When anti-malware software has removed the ransomware, you can safely access your backup to start recovering files.
Site Disclaimer
WiperSoft.com is not sponsored, affiliated, linked to or owned by malware developers or distributors that are referred to in this article. The article does NOT endorse or promote malicious programs. The intention behind it is to present useful information that will help users to detect and eliminate malware from their computer by using WiperSoft and/or the manual removal guide.
The article should only be used for educational purposes. If you follow the instructions provided in the article, you agree to be bound by this disclaimer. We do not guarantee that the article will aid you in completely removing the malware from your PC. Malicious programs are constantly developing, which is why it is not always easy or possible to clean the computer by using only the manual removal guide.