US Department of Justice revealed to be affected by SolarWinds hack
The US Department of Justice has been revealed to be among those affected by the massive SolarWinds hack. A short statement released by the Department of Justice Office of Public Affairs reveals that attackers were able to access the Department’s Microsoft O365 email server.
A statement issued by Department of Justice (DoJ) Spokesperson Marc Raimondi explains that the Department of Justice’s Office of the Chief Information Officer (OCIO) became aware of malicious activity linked to the SolarWinds cyber attack, and said activity involved access to the Department’s Microsoft O365 email environment. According to the statement, the OCIO was able to eliminate the method used to access the email server upon learning of the malicious activity, but the attacker was able to access around 3 percent of DoJ email accounts. Reportedly, it appears that classified systems were not impacted.
“After learning of the malicious activity, the OCIO eliminated the identified method by which the actor was accessing the O365 email environment. At this point, the number of potentially accessed O365 mailboxes appears limited to around 3-percent and we have no indication that any classified systems were impacted,” Marc Raimondi said.
The US Department of Justice is one of the many entities impacted by the massive SolarWinds cyber attack that came to light mid-December last year. Overall, around 18,000 government organizations and private companies have been potentially impacted by the cyber attack. Along with DoJ, among impacted US government agencies are:
- The US Department of State
- The Department of Homeland Security (DHS)
- The US Treasury Department
- The US Department of Energy (DOE)
- The National Nuclear Security Administration (NNSA)
- The Cybersecurity and Infrastructure Agency (CISA)
- The Department of Health’s National Institutes of Health (NIH)
- The US Department of Commerce’s National Telecommunications and Information Administration (NTIA)
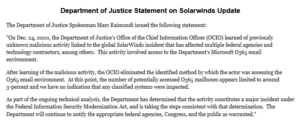 Statement released by the Department of Justice
Statement released by the Department of Justice
US has called the SolarWinds hack “Russian Intelligence Gathering Effort”
As reported yesterday, the US government has issued a statement in which Russia is named as the likely perpetrator behind the massive SolarWinds attack.
Four US government agencies, including Federal Bureau of Investigation (FBI), the Cybersecurity and Infrastructure Security Agency (CISA), the Office of the Director of National Intelligence (ODNI), and the National Security Agency (NSA), have also announced a special task force Cyber Unified Coordination Group (UCG) that was created specifically to investigate the incident and deal with the fallout. The same statement announcing the task force also calls the attacker “likely Russian in origin”.
“This work indicates that an Advanced Persistent Threat (APT) actor, likely Russian in origin, is responsible for most or all of the recently discovered, ongoing cyber compromises of both government and non-governmental networks. At this time, we believe this was, and continues to be, an intelligence gathering effort. We are taking all necessary steps to understand the full scope of this campaign and respond accordingly,” the statement reads.
The attack was publicly revealed mid-December, 2020 when cybersecurity company FireEye revealed that malicious actors were able to access the internal network of software firm SolarWinds and insert malicious code into update packages for Orion, a software used for IT monitoring. Malicious updates were pushed to customers between March and June, 2020. Out of 33,000 Orion customers, around 18,000 installed the updates containing the malicious code. However, only a small number of those who installed the update have been compromised by follow-up activity.
Site Disclaimer
WiperSoft.com is not sponsored, affiliated, linked to or owned by malware developers or distributors that are referred to in this article. The article does NOT endorse or promote malicious programs. The intention behind it is to present useful information that will help users to detect and eliminate malware from their computer by using WiperSoft and/or the manual removal guide.
The article should only be used for educational purposes. If you follow the instructions provided in the article, you agree to be bound by this disclaimer. We do not guarantee that the article will aid you in completely removing the malware from your PC. Malicious programs are constantly developing, which is why it is not always easy or possible to clean the computer by using only the manual removal guide.

