Cassiopesa.com Browser Virus – How to remove
What is Cassiopesa.com?
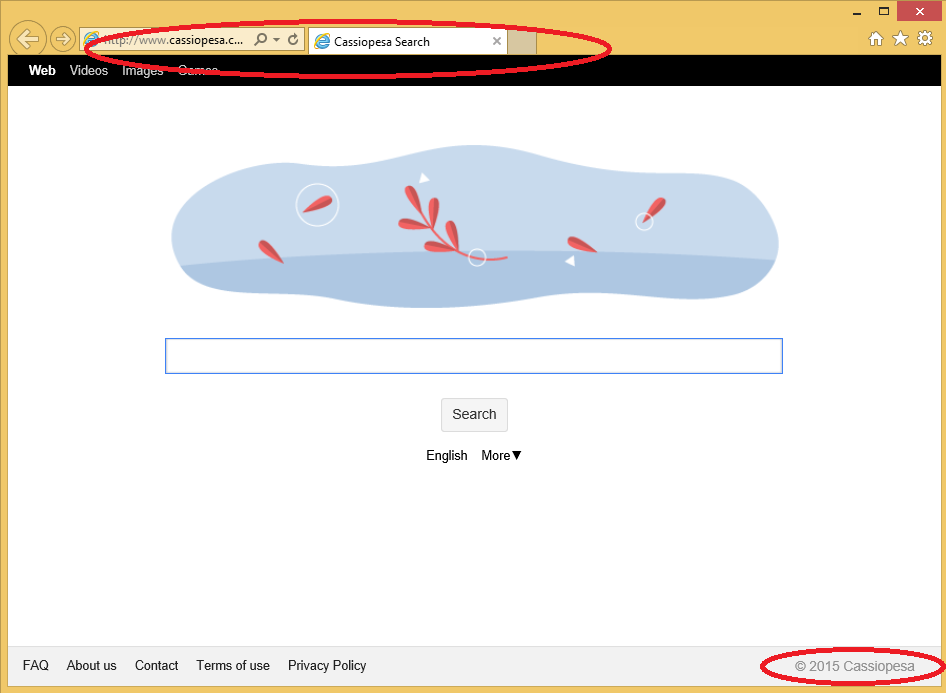
Cassiopesa.com is classified as a browser hijacker by many computer experts. Hijackers are computer’s parasites that were created in order to modify your browsers’ settings (home page, default search engine, new tab page) and to to direct traffic to the affiliate parties’ websites. To achieve this goal, Cassiopesa.com will present you with numerous ads and sponsored links making your search results completely untrustworthy. Furthermore, it was noticed that the hijacker may randomly redirect you to some suspicious websites in the middle of you browsing session. All these hindrances can prove to be very annoying and, most importantly, dangerous to your computer’s safety. Even if you attempt to avoid the intruder, you will not be successful, since the application infiltrates Internet Explorer, Mozilla Firefox, and Google Chrome browsers. Our research team prepared this article to explain to you in more detail why this software is so dangerous and what is the best way to get rid of Cassiopesa.com.
What does Cassiopesa.com do?
As we said, the first thing this intruder does once it enters a new computer is the changes in your home page and default search engine. In many cases, the unauthorized alterations are more than enough to convince users that the application that is currently residing in their systems is untrustworthy and that they have to eliminate it. Remember that these changes allow the software to modify user’s search results by adding a bunch of promoted links and ads in between them. Users frequently complain that they have a hard time filtering through the presented search results and that some of the links have nothing in common with their search query. The ads usually distract users from their browsing and are, actually, a big factor in convincing them to start looking for ways to terminate Cassiopesa.com . However, the irritation you feel over the ads and additional links is certainly not the main reason we advise to delete Cassiopesa.com.
The biggest problem associated with browser hijackers are the unknown and thus, unreliable third parties. Since nobody monitors those parties, there is no way to tell who stands behind them. This uncertainty means that you may enter a page controlled by cyber criminals after you click the suspicious ad, link or get redirected without a warning. Needless to say, such encounter is very risky and can have long-lasting and harmful consequences to your system. If you enter such a suspicious site, you will most likely get infected with malware. You must do everything to prevent such treats like virus, Trojan, worm, keylogger, etc. from entering your PC, since any one of them can devastate your computer and steal your information. We advise to remove Cassiopesa.com as soon as you can to minimize this risk.
Some users notice that the presented ads correspond very well with their latest searches. This can be explained by the tracking of your data this browser hijacker starts as soon as it enters your system. Such information like IP address, geographical location, search queries, browsing history, clicks, the time you spend in specific pages, preferred websites, etc. is known to the intruder and used in many ways. Firstly, the application uses the gathered knowledge to make the presented ads more appealing to you by personalizing them. This is supposed to increase the possibility that users will click the ads. However, it is also likely that the data will be shared with third parties which is not something you should tolerate. Remember that those parties are completely unknown and thus cannot be trusted. Basically, you will never know for what purposes your data will be used, since for as long as the hijacker stays in your system, almost anyone can access it. To stop this uncontrollable spread of your information, we recommend to eliminate Cassiopesa.com.
How did Cassiopesa.com enter your PC?
In the majority of cases, Cassiopesa.com sneaks into your computer alongside freeware. This deceptive marketing method is called ‘bundling’ and is used very often by the creators of the potentially undesirable software. If you often acquire applications from unofficial or suspicious sources, you should really learn how to better protect your PC. Since everyone knows that users do not monitor free software downloads, it becomes very easy for the potentially unwanted or even malicious programs to enter your system. In the future, we advise to always chose Advanced or Custom installation options. Either one of these options will guarantee you full control over the installation procedure. Also, do not forget to read the entire End Use License Agreement (EULA). In this document, you need to look for the boxes that announce additional progarms. When you notice them, click the Decline button. Do not allow some suspicious software to infiltrate your PC and if that already happened, uninstall Cassiopesa.com.
How to remove Cassiopesa.com?
We hope that this article convinced you that it is in the best interest of you computer to delete Cassiopesa.com. It should be obvious that the browser hijacker brings you no benefit, but puts your entire system at risk. The manner of its entrance alone should make you immediately distrustful of this software. Also, you must not forget the unauthorized changes and exposure to the pottetnially malicious parties. We urge you not to delay any longer and to remove Cassiopesa.com. To do that, you have two options available for you. If you wish to do everything by yourself, you should follow the manual instructions on how to erase Cassiopesa.com. However, if you prefer automatic Cassiopesa.com removal option, you should employ a legitimate and up-to-fate computer security software. Such tool will not only deal with your problem, but also will stay in your PC to protect it after Cassiopesa.com removal is complete.
Delete Cassiopesa.com
Uninstall from Windows 8
- Navigate to the bottom right corner of your desktop.
- Choose Settings.
- Click Control Panel.
- Open Uninstall a program.
- Uninstall Cassiopesa.com.
Uninstall from Windows XP
- Press Start button.
- Choose Control Panel.
- Pick Add or Remove programs.
- Remove Cassiopesa.com.
Uninstall from Windows Vista and Windows 7
- Open Start menu.
- Select Control Panel.
- Go to Uninstall a program.
- Remove Cassiopesa.com.
Erase Cassiopesa.com from your browsers
Delete Cassiopesa.com from Internet Explorer
- Click the Gear icon to open menu and choose Internet Options.
- Replace your current home page with a new one in the General tab.
- Press Gear icon one more time and access Manage Add-ons.
- Go to Toolbars and Extensions and delete unwanted add-ons.
- In Search Providers, overwrite your search engine.
Delete Cassiopesa.com from Google Chrome
- Tap the menu icon and open Settings.
- Choose Set pages and delete/change the home page.
- Under Search, select Manage search engine.
- Eliminate the old search tool and select another as your default.
- Go to Extensions and terminate useless add-ons.
Delete Cassiopesa.com from Mozilla Firefox
- Press the menu icon and select Options.
- Access General tab and replace your current home page with another.
- Move to Search tab and delete/change your search provider
- Tap the menu again and click Add-ons.
- Remove undesirable extensions.
Site Disclaimer
WiperSoft.com is not sponsored, affiliated, linked to or owned by malware developers or distributors that are referred to in this article. The article does NOT endorse or promote malicious programs. The intention behind it is to present useful information that will help users to detect and eliminate malware from their computer by using WiperSoft and/or the manual removal guide.
The article should only be used for educational purposes. If you follow the instructions provided in the article, you agree to be bound by this disclaimer. We do not guarantee that the article will aid you in completely removing the malware from your PC. Malicious programs are constantly developing, which is why it is not always easy or possible to clean the computer by using only the manual removal guide.
