Coos ransomware removal
Coos ransomware aims to encrypt your files and take them for hostage until you agree to pay a ransom. This ransomware is part of the notorious Djvu/STOP ransomware family, which is responsible for releasing more than two hundred ransomware versions.
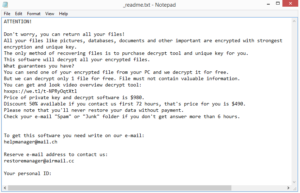 The ransom note dropped by Coos ransomware
The ransom note dropped by Coos ransomware
If your files suddenly have the .coos file extension, your files are likely encrypted with the Coos ransomware. It’s a dangerous piece of malware because it essentially takes files for hostage and demands a payment for their recovery. This particular malware is part of a large Djvu/STOP ransomware family and is one of the hundreds of versions. You can identify which one you’re dealing with by the extension added to encrypted files. In this case, .coos is added. You will not be able to open files with that extension, unless you decrypt them first. But to obtain a decryptor, you are asked to pay $980 (or $490 if contact is made with cyber crooks within the first 72 hours). The whole file recovery process is explained in the _readme.txt ransom note that’s dropped once the files are encrypted.
If you are considering paying the ransom, keep in mind that you are dealing with cyber criminals who will likely not be as helpful as you’d think. There’s nothing really stopping them from simply taking the money, considering there’s nothing obligating them to help. Many victims in the past have paid but received nothing in return. So before making a decision, consider that you could lose both your files and your money.
A lot of older Djvu versions are decryptable with various decryptors available for download. The Emsisoft Decryptor for STOP Djvu is one of them. However, it will not work on newer versions like Coos because they use online keys to encrypt files. That means that every victim has a unique key, which is necessary to develop a working decryptor.
If you have backup, you shouldn’t have any issues with file recovery, though you first need to remove Coos ransomware from the computer. Use anti-virus software to do that because ransomware is a complicated infections and dealing with it manually could cause even more damage.
Ransomware can enter a computer in a variety of ways
Ransomware can infect your computer in many different ways, including spam emails, torrents, fake updates, malicious ads, rootkits, etc. It’s much easier for it to infect a computer if you have bad browsing habits so we recommend you familiarize yourself with how to avoid malware.
One of the main ways ransomware usually enters is via spam email attachments. Malicious actors purchase thousands of emails from hacker forums and launch malspam campaigns using them. The malspam is fortunately very obvious in most cases as long as you don’t rush to open any emails from unknown senders. Look out for grammar and spelling mistakes, especially when the sender claims to be from some known company or government organization. No official email will contain grammar mistakes, as that looks unprofessional. Another sign is the sender’s email address being made up of random letters and numbers. As a precaution, we would recommend scanning all unsolicited email attachments with anti-virus software or VirusTotal before opening them.
Torrents are also often used to distribute malware, particularly ones for popular entertainment content. A lot of torrent sites are poorly regulated, which means malicious actors can upload torrents with malware in them. It’s especially common for torrents for popular movies, TV shows, games, etc., to contain malware. It’s strongly suggested to avoid pirating via torrents, if not because it’s stealing content, then because it’s dangerous for the computer.
You should also regularly install updates, or preferably turn on automatic updates. Updates patch known system vulnerabilities, which can be used by malware to get into the system. To avoid that from happening, always install updates as they’re released.
Coos ransomware demands $980 for file decryption
When Coos ransomware starts encrypting your files, it will show a fake Windows Update window to distract you from what’s going on. In the meantime, it will encrypt your photos, videos, documents, etc. File encryption can be instantaneous, and once it’s done, all your personal files will have .coos added to them. As an example, text.txt would become text.txt.coos. You will not be able to open any of the files that have this extension.
You will also find _readme.txt ransom note in all folders containing encrypted files. The note is the same one dropped by the other Djvu ransomware versions. It explains that files have been encrypted but you can recover them if you are willing to pay the ransom. The note explains that the regular price for the decryptor is $980, but a 50% discount would be provided if contact is made with the cyber crooks within the first 72 hours. The emails provided for contact are helpmanager@mail.ch and restoremanager@airmail.cc.
While it may appear that paying the ransom is a good idea but you should keep in mind that giving into the demands is risky. There are no guarantees that you will get the decryptor, provided you are dealing with cyber criminals. And $980 is a lot of money to lose.
At this moment, the only way to recover files is from backup. If you backed up files prior to the ransomware infection, you can easily recover files as soon as you delete Coos ransomware from the computer.
If you don’t have backup and have no way of recovering files, back up the encrypted files and wait for a free decryptor to become available in the future. Malware researchers do release free decryptors when possible but at this moment, one for Coos ransomware is not available. If one is released, it would be come available on NoMoreRansom.
Coos ransomware removal
You should be using anti-virus software to delete Coos ransomware, as it’s a complicated infection. Loads of anti-virus programs will detect and get rid of it, so you have a wide range of choices if you don’t have anti-virus installed at this moment. We don’t recommend trying manual Coos ransomware removal, as you could end up doing more damage.
Site Disclaimer
WiperSoft.com is not sponsored, affiliated, linked to or owned by malware developers or distributors that are referred to in this article. The article does NOT endorse or promote malicious programs. The intention behind it is to present useful information that will help users to detect and eliminate malware from their computer by using WiperSoft and/or the manual removal guide.
The article should only be used for educational purposes. If you follow the instructions provided in the article, you agree to be bound by this disclaimer. We do not guarantee that the article will aid you in completely removing the malware from your PC. Malicious programs are constantly developing, which is why it is not always easy or possible to clean the computer by using only the manual removal guide.
