Dehd ransomware removal
.dehd is the file extension added to files encrypted by Dehd ransomware. If your files suddenly have this extension and you cannot open them, they have been encrypted by ransomware. Dehd ransomware comes from a notorious malware family known as Djvu/STOP and is a very serious computer infection. Encrypted files will be unopenable unless you first use a decryptor on them. But obtaining that decryptor is difficult. The only people who currently have it are the ones operating this ransomware, and they will not be generous enough to just give it to you for free. And paying for it is risky because you could lose your money.
Dehd ransomware belongs to the notorious Djvu/STOP ransomware family. The cybercrime gang operating this ransomware releases ransomware on a regular basis, though they are more or less identical. If you’re attacked by ransomware from this family, you can identify which version you are dealing with by the extension added to encrypted files. As we already mentioned, if you find .dehd attached to your files, your computer is infected with Dehd ransomware. The ransomware will have encrypted all of your personal files, including photos, images, videos, documents, etc. As an example, an encrypted image.jpg file would become image.jpg.dehd. You will not be able to open any of these files unless you are able to acquire a decryptor.
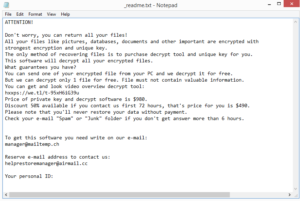
The cybercriminals operating this ransomware will offer you the decryptor for money, and it’s explained in the _readme.txt ransom note dropped in all folders that contain encrypted files. The note is generic but it does contain information on how to get the decryptor. Unfortunately, the cybercriminals operating this ransomware are demanding $980 for the decryptor. The note does mention that those who make contact within the first 72 hours will get a 50% discount but whether that is actually true is questionable. We also don’t recommend paying the ransom. While the decision is yours to make, there are certain risks you need to be aware of. The most important thing to mention is that there are no guarantees you will receive the decryptor even after paying. You are dealing with cybercriminals, what’s there to stop them from simply taking the money but not sending the decryptor. Considering that they are the ones developing/distributing ransomware, they are unlikely to feel obligated to help victims, even the ones who pay. Furthermore, one of the reasons ransomware has become so widespread is because victims pay the ransom.
For users with a habit of backing up important files, file recovery shouldn’t be an issue. However, it’s important to first fully delete Dehd ransomware from the computer. If you connect to your backup while ransomware is still present, it would encrypt your backed-up files as well. Thus, we highly recommend using anti-virus software to remove Dehd ransomware. Do not try manual removal because you could end up causing more damage.
When there is no backup, file recovery is much more complicated. Malware researchers and security specialists are sometimes able to release free decryptors to help victims but in this case, it’s difficult. Dehd ransomware and most ransomware from this family use online encryption keys, which means that each victim has a unique key. Without those keys, the chances of developing a working decryptor are slim. You can find a free Djvu/STOP decryptor released by Emsisoft but it’s unlikely to work on Dehd ransomware. There is no harm in trying, however.
How did ransomware enter your computer?
Malicious emails, also known as malspam, are a very common way malicious actors distribute their malware. It’s a pretty low-effort and quite a convenient method. Threat actors buy victims’ email addresses from all kinds of hacker forums and send them malicious emails in hopes users will open the attached files. Once the file is opened, the malware can initiate. Fortunately for you, if you learn to recognize malicious emails, you will be able to avoid a lot of malware. Malicious emails are usually full of grammar and spelling mistakes despite senders claiming to be emailing on behalf of some company whose services you use. And such emails also address users in generic terms like “User”, “Member”, “Customer”, even when they claim you use their services and they should know your name. Legitimate emails sent by companies whose services you use will never contain mistakes, and you will always be addressed by your name or the name you have given them. In some cases, malspam is more sophisticated, so we recommend always scanning unsolicited email attachments with anti-virus software before opening them.
Pirating copyrighted content via torrents is often discouraged not only because it’s essentially stealing but also because it’s dangerous for the computer and your data. In case you are not aware of this, torrent sites are often poorly regulated. This allows cybercriminals to easily upload malicious content but disguise it as a torrent for something popular like a movie, TV show, video game, software, etc. For example, whenever a new Marvel movie is released, torrents for it will more often than not contain malware. So we advise against pirating.
These are just two of the more common ways ransomware is distributed. You can also pick up infections by downloading content from unreliable sources, clicking on ads, frequenting high-risk websites, etc. If you take the time to develop good browsing habits, you will be able to avoid a lot of malware.
Dehd ransomware removal
When it comes to ransomware removal, it’s always recommended to use anti-virus software. Make sure to use reliable anti-virus to delete Dehd ransomware. And do not connect your backup unless you are absolutely sure the ransomware is gone.
Once you’ve taken care of the ransomware, proceed to recover files from your backup. If you do not have a backup, one option is to back up encrypted files and wait for a free decryptor to become available. NoMoreRansom is a good source to check for free decryptors.
Site Disclaimer
WiperSoft.com is not sponsored, affiliated, linked to or owned by malware developers or distributors that are referred to in this article. The article does NOT endorse or promote malicious programs. The intention behind it is to present useful information that will help users to detect and eliminate malware from their computer by using WiperSoft and/or the manual removal guide.
The article should only be used for educational purposes. If you follow the instructions provided in the article, you agree to be bound by this disclaimer. We do not guarantee that the article will aid you in completely removing the malware from your PC. Malicious programs are constantly developing, which is why it is not always easy or possible to clean the computer by using only the manual removal guide.