Delete Irfk ransomware
Irfk ransomware is a generic ransomware infection from the Djvu/STOP ransomware family. It’s the most recent ransomware to be released by this cyber gang, one of the hundreds of mostly identical ransomware. The ransomware encrypts files and adds .irfk to them, which is how you can identify which ransomware you’re dealing with. Unfortunately, you will not be able to open any of those files, unless they are first decrypted. But there currently is no free Irfk ransomware decryptor available.
Irfk ransomware comes from the same ransomware family as Palq, Cool, Rivd, and Rugj. The cyber gang operating these ransomware infections has been actively releasing new versions for years, with a release every couple of days. There currently are hundreds of these file-encrypting malware infections. They all target personal files, including photos, videos, images, documents, etc. Files encrypted with this ransomware will have .irfk attached to them, and you will be unable to open them. To give an example, image.jpg would become image.jpg.irfk.
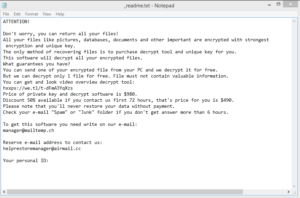
While the ransomware is encrypting your files, it will show a fake Windows update window. And once file encryption is done, all folders containing encrypted files will have _readme.txt ransom notes. The note contains information on how to obtain the decryptor, which unfortunately means paying $980 in ransom. The note also mentions that those who make contact with the cybercriminals within the first 72 hours would receive a 50% discount. However, paying is still not recommended. Keep in mind that you are dealing with cybercriminals and there is nothing to ensure that you will get a decryptor. Countless victims have paid in the past but received nothing in return. Whether you pay or not is your decision but you need to be aware of the risks involved.
If you have a backup, you should have no issues with recovering files. As long as you remove Irfk ransomware before you connect your backup, you should be able to restore everything. However, keep in mind that if the ransomware is still present when you connect to your backup, your backed-up files would become encrypted as well.
If you do not have a backup, your only option is to back up encrypted files and wait for a free decryptor to become available. It may be difficult to develop a free one because ransomware threats in this family use online keys to encrypt files. This means that all victims have unique keys, and without those keys, it’s difficult to develop a decryptor. There is a free Djvu/STOP decryptor developed by Emsisoft but it will not work on the majority of ransomware released after 2019. If you try to look for decryptors, be careful to not download malware instead. There are many fake decryptors promoted on various questionable forums but keep in mind that if you cannot find it on legitimate sites like NoMoreRansom, decryptors on random forums are likely to do more harm than good.
Ransomware distribution methods
In addition to securing your computer and regularly backing up files, it’s important to have good browsing habits. Simple actions like opening email attachments, downloading torrents, or clicking on ads when visiting high-risk websites could lead to serious malware infections.
One of the most common ways victims pick up malware infections is via spam email attachments. For a computer to become infected, it’s enough for users to open malicious attached files. The files usually come attached to emails that are made to appear like they’re sent from legitimate senders whose services users use. However, in most cases, these attempts are very poor. For example, senders claim to be from legitimate companies but the emails contain a significant amount of grammar and spelling mistakes. Grammar mistakes are very rare in official correspondence because it makes a company look unprofessional. But whether it’s intentional or not, malicious emails are always full of them. Another thing to pay attention to when dealing with unsolicited emails that have attachments is how you are addressed. If the sender claims that you use their services, check whether you are addressed by name. If you actually use their services, you will be addressed by your name. If generic terms like User, Member, Customer, etc., are used, it could be a sign of a malicious email. While most malicious emails will be quite obvious in many cases, some targeted attacks can be quite sophisticated. Thus, it’s highly recommended to use VirusTotal or anti-virus programs to scan all unsolicited email attachments.
If you are one to pirate copyrighted content via torrents, you will have encountered malware sooner or later. Torrent sites are often poorly regulated, which cyber criminals take full advantage of by uploading malicious content in torrents for popular movies, TV shows, video games, software, etc. In particular, malware is often found in torrents for recently released content. For example, if you were to check torrents for recently released Marvel movies, the majority of them would have malware in them. Not only is pirating essentially stealing content, but it also puts your computer and data at risk.
Irfk ransomware removal
Considering that ransomware is a very dangerous malware infection, it’s not a good idea to try to remove Irfk ransomware manually. You could end up causing even more damage if you’re not careful, or you may not fully eliminate the infection, thus allowing it to recover. If, when you connect to backup, the ransomware is still there, your backed-up files would become encrypted as well. Thus, we recommend using anti-malware software to delete Irfk ransomware. Only when it’s fully gone is it safe to access your backup.
If you do not have a backup, we recommend backing up the encrypted files and occasionally checking NoMoreRansom for a decryptor. Keep in mind that if you cannot find a decryptor on legitimate sites like NoMoreRansom, the decryptor you may find on a random forum will likely be fake or distribute more malware.
Site Disclaimer
WiperSoft.com is not sponsored, affiliated, linked to or owned by malware developers or distributors that are referred to in this article. The article does NOT endorse or promote malicious programs. The intention behind it is to present useful information that will help users to detect and eliminate malware from their computer by using WiperSoft and/or the manual removal guide.
The article should only be used for educational purposes. If you follow the instructions provided in the article, you agree to be bound by this disclaimer. We do not guarantee that the article will aid you in completely removing the malware from your PC. Malicious programs are constantly developing, which is why it is not always easy or possible to clean the computer by using only the manual removal guide.