How to remove Vtym ransomware
Vtym ransomware is file-encrypting malware from the Djvu/STOP ransomware family. The majority of ransomware versions from this malware family are more or less identical, though they can be differentiated by the extensions added to encrypted files. This ransomware adds .vtym, hence why it’s known as Vtym ransomware. Unfortunately, you will not be able to open any files with this extension unless you first use a decryptor on them. But acquiring the decryptor will be problematic because the only people who have it are the cybercriminals operating this ransomware. And they will not simply give it to you. Rather, they will try to sell you the decryptor. But buying comes with its own risks.
If you’ve encountered ransomware from this family in the past, you may notice that Vtym ransomware is practically identical to most newer Djvu/STOP versions. These versions can be differentiated by the extensions added to encrypted files. This one adds .vtym, hence why it’s known as Vtym ransomware. For example, an encrypted text.txt file would become text.txt.vtym. All of your personal files, including photos, videos, images, and documents will have this extension because they are the target files. You will not be able to open any of these files unless you first use a decryptor on them. The ransom note will explain how you can get the decryptor.
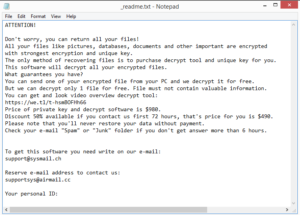
During file encryption, the ransomware will display a fake Windows update window, likely to distract users from what’s going on. Once files are fully encrypted, the ransomware will drop ransom notes in all folders containing encrypted files. The _readme.txt ransom note is pretty generic and contains only basic information. It does explain how users can get the decryptor though. According to the note, users need to pay $980 to get a decryptor. It’s also mentioned that those who make contact within the first 72 hours will receive a 50% discount. Whether the discount is true or not, paying the ransom is still not recommended. There are no guarantees that you will get the decryptor, considering that you are dealing with cybercriminals. It’s unlikely that they will feel any kind of obligation to help since they were the ones who encrypted your files in the first place. Unfortunately, there have been countless users who have not received their decryptors despite paying.
The chances of recovering files are significantly lower if you do not have a backup. If you’re not planning on paying the ransom, waiting for a free decryptor to become available may be your only option. The thing is, developing a working decryptor for Vtym ransomware will be difficult because the ransomware uses online keys to encrypt files. This means that the keys are unique to each user, and unless those keys are released by the cybercriminals themselves (not impossible), a free decryptor is not likely. There is a free Djvu/STOP decryptor released by Emsisoft but it only works on ransomware whose encryption keys Emsisoft has. So it’s unlikely to work on files encrypted by Vtym ransomware. Nonetheless, you should back up your encrypted files and occasionally check NoMoreRansom for a free decryptor.
If you have copies of your files stored somewhere in a backup, do not try to access them before you completely delete Vtym ransomware from your computer. If the ransomware is still present when you access your backup, your backed-up files would become encrypted as well. So before you do anything, make sure to get rid of the ransomware first using anti-malware software.
How does ransomware infect computers?
When it comes to ransomware, cybercriminals use all kinds of methods to distribute it. The most common methods include malicious spam emails, torrents, ads, etc. Generally, users who have bad browsing habits are at a much higher risk of picking up malware infections. Taking the time to develop better browsing habits can significantly lower the chances of a malware infection.
Malicious spam, or malspam in short, is a very common method used by cybercriminals to distribute malware. It’s doesn’t require much effort on their side because all they need to do is purchase email addresses from hacker forums and spam them with semi-convincing emails that contain malicious attachments. Once users open those attachments, the malware can initiate. Fortunately for users, these emails are fairly obvious. Malicious senders claim to be legitimate companies whose services users use but use generic terms (e.g. User, Member, Customer, etc.) to address users. You likely have noticed that when a legitimate company emails you, it uses the name you have given them to address you. For example, if you’re a Netflix user, all emails will address you with the name used for the primary profile. The names are added automatically to even the most generic emails. So if someone who should know your name sends you an unsolicited email but addresses you generically, that should cause suspicion. Another sign is grammar and spelling mistakes. For whatever reason, the majority of malicious emails have countless mistakes in them. But even when an email looks completely legitimate, it’s still not a good idea to open unsolicited email attachments without first double-checking them. You can scan them using your anti-virus software or VirusTotal.
Pirating copyrighted content using torrents is also a very easy way to pick up malware infections. You’re likely already aware of this but torrent sites are quite poorly regulated. This allows malicious actors to upload malware quite easily. If you pirate via torrents, you’re not only essentially stealing content but also putting your computer/date in danger.
Vtym ransomware removal
Considering that ransomware is a pretty complex malware infection, it’s not a good idea to try to remove Vtym ransomware manually. If you’re reading this, you likely do not have enough experience to fully get rid of the ransomware. To avoid additional damage, we would strongly recommend using reliable anti-malware software. Once the ransomware is no longer on your computer, you can safely connect to your backup and start recovering your files. If you do not have copies of your files, back up the encrypted files in case a decryptor is ever released.
Site Disclaimer
WiperSoft.com is not sponsored, affiliated, linked to or owned by malware developers or distributors that are referred to in this article. The article does NOT endorse or promote malicious programs. The intention behind it is to present useful information that will help users to detect and eliminate malware from their computer by using WiperSoft and/or the manual removal guide.
The article should only be used for educational purposes. If you follow the instructions provided in the article, you agree to be bound by this disclaimer. We do not guarantee that the article will aid you in completely removing the malware from your PC. Malicious programs are constantly developing, which is why it is not always easy or possible to clean the computer by using only the manual removal guide.