What is Jzie Ransomware? How It Works and How to Remove It
What is Jzie Ransomware
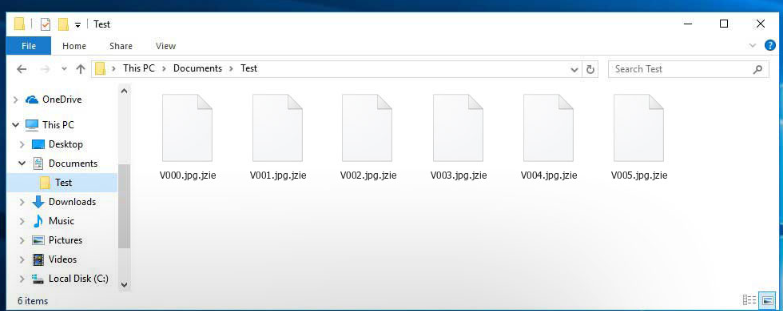
Jzie is a Windows ransomware infection that was released in the middle of September 2023. This ransomware infection will affect all versions of Windows, including Windows XP, Windows Vista, Windows 7, Windows 8, and Windows 10. When a victim is infected they will have their files encrypted and then a ransom of about .5 bitcoins will be demanded in order to receive the decryption key. Jzie alters file names using this pattern: it changes a file named “1.jpg” to “1.jpg.jzie”, “2.png” to “2.png.jzie”, and so on. It is essential to highlight that Jzie is a member of the Djvu ransomware family. Frequently, cybercriminals distribute Djvu ransomware in tandem with data-stealing malware, such as RedLine or Vidar.
The ransom price for obtaining the private key and decryption software is set at $980. However, the attacker extends a 50% discount if the victim makes contact within the first 72 hours, reducing the price to $490. In order to acquire the decryption tool, the victim is instructed to contact the perpetrator using support@freshmail.top or datarestorehelp@airmail.cc email address.
Why would people who locked your data the first place help you recover them when there is nothing stopping them from just taking your money. Furthermore, your money would also support their future malware projects. Do you really want to support the kind of criminal activity. The more people pay, the more profitable it gets, thus luring more malevolent parties to it. Situations where you could lose your files are pretty typical so backup would be a better purchase. If you had backup available, you could just terminate Jzie Ransomware virus and then restore files without being worried about losing them. You can find info on how to safeguard your system from this threat in the below paragraph, if you’re not certain about how the data encoding malware even got into your device.
How does Jzie ransomware spread
Rather basic ways are used for spreading ransomware, such as spam email and malicious download scracking tools, key generators, and deceptive pages offering to download videos from YouTube or emails containing malicious attachments or links. A rather big number of data encrypting malicious programs depend on user carelessness when opening email attachments and more sophisticated methods are not necessary. That isn’t to say that distributors do not use more sophisticated methods at all, however. Crooks don’t need to do much, just write a simple email that less cautious users may fall for, attach the infected file to the email and send it to hundreds of people, who may believe the sender is someone trustworthy. Money related issues are a common topic in those emails since people tend to engage with those emails. It’s quite often that you will see big company names like Amazon used, for example, if Amazon emailed someone a receipt for a purchase that the person does not remember making, he/she would open the attached file immediately. When you are dealing with emails, there are certain signs to look out for if you want to secure your computer. Check if the sender is known to you before opening the file attached to the email, and if you do not know them, investigate who they are. And if you do know them, check the email address to make sure it’s really them. Also, look for mistakes in grammar, which generally tend to be quite obvious. Take note of how you’re addressed, if it’s a sender who knows your name, they’ll always use your name in the greeting. Vulnerabilities on your system Out-of-date software may also be used as a pathway to you computer. A program comes with vulnerabilities that could be exploited by ransomware but usually, they’re fixed when the vendor becomes aware of it. However, judging by the amount of systems infected by WannaCry, obviously not everyone rushes to install those updates. It is very crucial that you regularly update your software because if a weak spot is serious enough, it could be used by malware. You can also make updates install automatically.
How does Jzie ransomware behave
Soon after the data encoding malware gets into your system, it will look for specific file types and once they have been found, it will encrypt them. Initially, it might be confusing as to what is going on, but when you are unable to open your files, it should become clear. A weird extension will also be attached to all affected files, which could help pinpoint the right ransomware. Your files may have been encoded using strong encryption algorithms, and it is likely that they might be permanently encrypted. You’ll be able to notice a ransom note which will explain what has occurred and how you ought to proceed to restore your files. Their suggested method involves you buying their decryptor. A clear price ought to be displayed in the note but if it is not, you will have to email hackers via their given address. Just as we mentioned above, we don’t suggest giving into the demands.
ATTENTION! Don’t worry, you can return all your files! All your files like pictures, databases, documents and other important are encrypted with strongest encryption and unique key. The only method of recovering files is to purchase decrypt tool and unique key for you. This software will decrypt all your encrypted files. What guarantees you have? You can send one of your encrypted file from your PC and we decrypt it for free. But we can decrypt only 1 file for free. File must not contain valuable information. You can get and look video overview decrypt tool: hxxps://we.tl/t-TAbs6oTGSU Price of private key and decrypt software is $980. Discount 50% available if you contact us first 72 hours, that’s price for you is $490. Please note that you’ll never restore your data without payment. Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours. To get this software you need write on our e-mail: support@freshmail.top Reserve e-mail address to contact us: datarestorehelp@airmail.cc Your personal ID:
Paying should be your last course of action. Try to recall whether you recently made copies of files but forgotten. Or, if luck is on your side, a free decryptor might be available. Malware researchers could sometimes release free decryption utilities, if the file encrypting malicious software is crackable. Keep this in mind before paying the ransom even crosses your mind. Using the demanded sum for a credible backup could do more good. And if backup is an option, you may restore data from there after you erase Jzie Ransomware virus, if it still remains on your computer. If you want to safeguard your device from file encoding malware in the future, become familiar with likely means via which it could get into your system. You primarily need to keep your software updated, only download from secure/legitimate sources and not randomly open email attachments.
Jzie Ransomware removal
If the data encrypting malicious program still remains, you’ll need to get a malware removal tool to terminate it. If you try to uninstall Jzie Ransomware virus in a manual way, you could end up harming your device further so that isn’t recommended. So as to prevent causing more damage, go with the automatic method, aka a malware removal program. A malware removal program is designed for the purpose of taking care of these kinds of infections, depending on which you have decided on, it could even prevent an infection. So research what matches your requirements, install it, scan your computer and ensure to get rid of the ransomware, if it is found. It ought to be said that a malware removal software will only eliminate the threat, it won’t unlock Jzie Ransomware files. After the file encrypting malware is entirely eliminated, it is safe to use your system again.
Site Disclaimer
WiperSoft.com is not sponsored, affiliated, linked to or owned by malware developers or distributors that are referred to in this article. The article does NOT endorse or promote malicious programs. The intention behind it is to present useful information that will help users to detect and eliminate malware from their computer by using WiperSoft and/or the manual removal guide.
The article should only be used for educational purposes. If you follow the instructions provided in the article, you agree to be bound by this disclaimer. We do not guarantee that the article will aid you in completely removing the malware from your PC. Malicious programs are constantly developing, which is why it is not always easy or possible to clean the computer by using only the manual removal guide.
