Delete Nooa ransomware
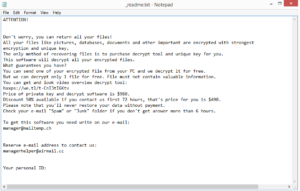
Nooa ransomware will encrypt your files and demand that you pay a ransom to recover them. It comes from the notorious Djvu/STOP malware family and is one of the hundreds of versions that these cybercrooks have released in only a couple of years. This version can be differentiated from the other ones by the .nooa file extension that gets added to encrypted files. It also drops the _readme.txt ransom note, which explains how to go about purchasing the decryptor.
Nooa ransomware is one of many ransomware versions released by the notorious Djvu/STOP ransomware family. The group is responsible for ransomware such as Hhqa, Ufwj, and Moqs. They are all more or less the same besides the file extension they add to encrypted files. This particular ransomware adds .nooa, hence why it’s known as Nooa ransomware.
The ransomware mainly targets personal files, including photos, videos, images, and documents. It’s easy to tell which files are encrypted because of the extensions. For example, image.jpg would become image.jpg.nooa. You will not be able to open these files unless you first run them through a decryption tool, which, unfortunately, is in the hands of cybercriminals operating this ransomware. Once the encryption process is complete, the ransomware will drop a _readme.txt ransom note. The note, which is shown above, explains that files have been encrypted and that the only way to decrypt them is to purchase a decryptor for $980 (or $490 if contact is made within the first 72 hours). These claims are, unfortunately, true at the moment. However, that does not mean that paying the ransom is a good idea. Keep in mind that you are dealing with cybercriminals who encrypted your files in the first place. There are no guarantees that you will receive the decryptor even after paying, as they can just take your money and not send anything in return. Many users in the past have not received their decryptors, so while the decision of whether to pay is yours, you should be aware of the risks.
If you have a backup of your files, there should be no issue with recovery. However, you need to first make sure to fully delete Nooa ransomware from the computer, as otherwise, the ransomware will encrypt the files in backup as well. This is one of the reasons why using anti-malware software is recommended for Nooa ransomware removal.
If you do not have a backup, your file recovery options are limited. There is the option of backing up encrypted files and waiting for a free decryptor to be released. Emsisoft has released a free Djvu/STOP decryptor back in 2019 but it will only work on versions that use offline keys for file encryption, meaning the keys are identical to all users and if one victim pays the ransom and gets the decryptor, it would work for other victims as well. However, Djvu/STOP versions released after 2019 usually use online keys for file encryption, meaning the key is unique for each victim. This prevents malware researchers from releasing a universal decryptor that would work for all victims. However, all hope is not lost, as the keys may be released by the cybercrooks themselves when they close shop, or by law enforcement if they ever catch the malware operators. So if you are out of options, back up your files and check NoMoreRansom for a decryptor on a regular basis.
To prevent even more infections in the future, we strongly recommend you read the below-provided information and familiarize yourself with how ransomware is distributed.
Ransomware distribution methods
Nooa ransomware doesn’t use any new or particularly interesting distribution methods. It mainly spreads via spam email attachments, fake updates/downloads, torrents, and malicious ads. It’s usually users’ bad browsing habits that lead to infections, so developing better ones can help prevent ransomware from entering your computer.
Because malware is so often spread via email attachments, you have a much higher chance of picking up an infection if you open unsolicited email attachments without first checking them. Malicious actors purchase thousands of email addresses from hacker forums and use them to launch malspam campaigns that spread malicious email attachments. Fortunately, unless someone is targeted specifically, the emails are usually pretty obvious. When you receive an unsolicited email that contains an attachment or link, always check the contents of the email before engaging further. Take note of the sender’s email address. If it looks random but the email is supposed to be some kind of official correspondence, be very skeptical. Pay attention to the grammar and spelling mistakes. Whether it’s done purposely or not, malicious emails are often full of them. Keep in mind that if a company whose services you use sends you an email, they will always address you by name. If you are addressed as User, Member, Customers, etc., by someone who should know your name, that’s a red flag as it would look unprofessional in an official email. It’s also a good idea to scan all unsolicited email attachments with anti-virus software or VirusTotal before opening them.
You’re also at increased risk of picking up malware if you pirate content via torrents. Torrent sites are often badly regulated, which allows malicious actors to easily upload malware disguised as movies, TV shows, video games, software, etc. It’s especially common to find malware in torrents for content that’s particularly popular. For example, when the popular TV series Breaking Bad was airing, torrents for episodes often had malware in them. You are discouraged from pirating, not only because it’s essentially stealing content but also because it’s dangerous for the computer.
Malware can also spread via malicious ads so it’s not a good idea to interact with any ads while browsing high-risk websites. You should also be careful of fake update alerts as those are known to spread various unwanted and potentially malicious programs.
Nooa ransomware removal
Ransomware is considered to be one of the most serious malware infections, hence why it’s not a good idea to try and remove Nooa ransomware manually. You could end up causing even more damage or not remove the ransomware fully, allowing the infection to recover. Use anti-virus software to delete Nooa ransomware, and only when the ransomware is fully gone should you connect to your backup to start recovering files. If ransomware is still present when you connect to backup, those files may become encrypted as well.
Unfortunately for those who do not have a backup, files will not automatically be decrypted just because you delete Nooa ransomware from the computer. As we mentioned already, a decryptor is necessary for that. If there are no other options left, we recommend users back up encrypted files and occasionally check NoMoreRansom for a free decryptor.
Site Disclaimer
WiperSoft.com is not sponsored, affiliated, linked to or owned by malware developers or distributors that are referred to in this article. The article does NOT endorse or promote malicious programs. The intention behind it is to present useful information that will help users to detect and eliminate malware from their computer by using WiperSoft and/or the manual removal guide.
The article should only be used for educational purposes. If you follow the instructions provided in the article, you agree to be bound by this disclaimer. We do not guarantee that the article will aid you in completely removing the malware from your PC. Malicious programs are constantly developing, which is why it is not always easy or possible to clean the computer by using only the manual removal guide.