Delete Pola ransomware
Pola ransomware encrypts files and takes them for hostage in exchange for $980 in ransom. It’s part of the Djvu/STOP ransomware family, which is responsible for releasing hundreds of other versions, including the recent Coos and Wbxd. This ransomware is differentiated by the .pola file extension added to encrypted files.
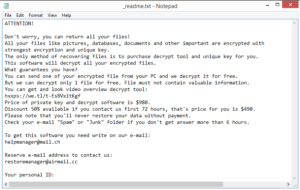 Ransom note dropped by this ransomware
Ransom note dropped by this ransomware
The Djvu/STOP ransomware family has been releasing ransomware left and right for over two years, and is responsible for infecting thousands of users. Djvu ransomware versions can be identified by the file extensions added to encrypted files. The recent one adds .pola, which is why it’s known as Pola ransomware. Once it’s initiated on a computer, the malware will encrypt files, essentially taking them for hostage until you agree to pay a ransom.
Once the files are encrypted, you will not be able to open them unless you first decrypt them. Unfortunately, the only ones who have the decryption tool are the malicious actors operating this ransomware. They will offer to send it to you, provided you are willing to pay $980 (or $490 if you contact them within 72 hours) in ransom. The whole file recover process will be explained in the _readme.txt ransom note dropped in all folders containing encrypted files. They even offer to decrypt one file for free if it doesn’t contain any important information. However, when it comes to cyber criminals and data decryption, it’s best to keep in mind that just because they can does not mean they will. Unfortunately, there are countless users who have paid the ransom but received nothing in exchange. So while you are the one to make the decision whether to pay or not, you should be aware of the risks in advance.
If you are in the habit of regularly backing up your files, you should have no issue with file recovery. However, before you access your backup, you need to first delete Pola ransomware from the computer. Otherwise, the ransomware would encrypt backed up files as well. Use anti-malware software to remove Pola ransomware and only then access your backup.
Older Djvu/STOP ransomware versions have a decryptor released by anti-virus company Emsisoft but it does not work on new versions, which unfortunately includes Pola ransomware as well. The reason is that new versions use online keys to encrypt files, meaning the keys are different for each user. The online key is necessary to have a working decryptor but the cyber crooks behind the ransomware are the only ones who have it. It is possible that the keys will be released, either by the cyber crooks themselves or by law enforcement, so it’s not impossible that a free decryptor will be released sometime in the future. But until then, do not trust questionable forums and sites that claim to have a working Pola ransomware decryptor. If one was to be released, it would be posted on NoMoreRansom.
How does ransomware infect a computer?
In most cases, users pick up infections like ransomware because of their bad browsing habits. If you open unsolicited email attachments without double-checking, pirate via torrents, not install updates, interact with questionable high-risk websites, etc., you have a high chance of picking up some kind of malware infection.
If you pirate copyrighted content, especially via torrents, you will likely pick up an infection eventually. Torrent sites are often not regulated properly, which means that malware distributors can easily upload malware as a torrent for a popular movie, episode of a TV show, game or software. Pirating is not only stealing content, it’s also quite dangerous for the computer.
Another common malware distribution method is email attachments. Malicious actors buy thousands of email addresses from hacker forums and use them to launch malspam campaigns which distribute malware. The emails are harmless as long as you don’t open the email attachments. In most cases, the malspam will be quite obvious so you should be able to recognize it before it’s too late. When dealing with an unsolicited email, check for grammar and spelling mistakes, and double-check that the sender’s email address is legitimate. The emails also usually pressure users to open the attachments by claiming they’re important documents that need to be reviewed. You should be able to avoid even the most sophisticated malspam if you scan all unsolicited email attachments with anti-virus software or VirusTotal.
Lastly, we highly recommend installing updates as they come out or enabling automatic updates. Updates patch known software vulnerabilities that can be used by malware to infect a computer, so installing them is very important.
How harmful is Pola ransomware?
As soon as you initiate the ransomware, it will start encrypting your documents, photos, videos, etc. While it’s doing that, it will show a fake Windows update window to distract you. It doesn’t take long to encrypt files, and once it’s done you will see .pola attached to them. This attachment indicates that the file has been encrypted. For example, text.txt would become text.txt.pola. You will not be able to open any encrypted files until you use a decryptor to restore them.
All folders that have encrypted files will have a _readme.txt ransom note in them. The note is identical to the ones dropped by other versions from this malware family. It first explains that files have been encrypted but can be recovered if a ransom is paid. One file can be decrypted if it doesn’t contain important information but paying $980 would be necessary to restore the rest of the files. Supposedly, if you contacted them within 72 hours, you would receive a 50% discount. The contact email addresses are helpmanager@mail.ch and restoremanager@airmail.cc. If you were to contact them, you would need to include the ID assigned to you (shown in the ransom note). However, as we said already, we don’t recommend paying the ransom as it does not guarantee that files will be decrypted.
Pola ransomware removal
Ransomware is a complicated malware infection, which is why you should be using anti-virus software to delete Pola ransomware. If you try to manually remove Pola ransomware, you could cause even more damage. Once the ransomware is no longer present, you can start file recovery if you have backup.
Site Disclaimer
WiperSoft.com is not sponsored, affiliated, linked to or owned by malware developers or distributors that are referred to in this article. The article does NOT endorse or promote malicious programs. The intention behind it is to present useful information that will help users to detect and eliminate malware from their computer by using WiperSoft and/or the manual removal guide.
The article should only be used for educational purposes. If you follow the instructions provided in the article, you agree to be bound by this disclaimer. We do not guarantee that the article will aid you in completely removing the malware from your PC. Malicious programs are constantly developing, which is why it is not always easy or possible to clean the computer by using only the manual removal guide.
