Hoop Ransomware removal
Hoop Ransomware is file-encrypting malware from the Djvu/STOP ransomware family. The group has released hundreds of ransomware versions, with Hoop being one of the more recent ones. This particular ransomware adds the .hoop file extension to encrypted files and drops the generic _readme.txt ransom note that explains how files could be decrypted. Unfortunately, at this moment the only ones with a working decryptor are the people operating this ransomware, thus making free decryption not possible at this time.
The Djvu/STOP ransomware group is notorious for releasing new ransomware on a regular basis. Some of the more recent and more widespread versions are Muuq, Nooa, Hhqa, Ujwj, and Moqs. They are more or less identical to one another but can be differentiated by the extensions that get added to encrypted files. If your computer is infected with Hoop ransomware, your files will have .hoop added to them. As you have probably noticed, these files are unopenable. And they will remain that way unless you run them through a specific decryptor. But unfortunately, the only ones with a working decryptor are the ones behind this ransomware.
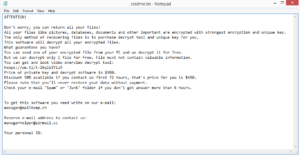
The whole file encryption process is very quick, with little chance to stop it once it begins. When the malicious file is opened and the ransomware is initiated, a fake Windows Update window will pop up in order to distract victims from the fact that their files are in the process of being encrypted. Once the encryption process is complete, personal files like photos, videos, documents, and images will be encrypted. For example, image.jpg would become image.jpg.hoop. A _readme.txt ransom note would also be dropped in all folders containing encrypted files. The note explains that files have been encrypted and that decryption is only possible via the decryptor they are selling. The price of the decryption tool depends on how quickly the cybercriminals are contacted. The regular price is $980 but if contact is made within 72 hours, a 50% discount would be applied. This is the standard price and discount that is mentioned in every ransom note dropped by ransomware from the Djvu/STOP malware family. manager@mailtemp.ch and managerhelper@airmail.cc are the contact email addresses given in the ransom note.
It should be said that it’s currently not possible to decrypt files without that decryptor. Nevertheless, paying the ransom is not recommended. If you are considering paying, keep in mind that you are dealing with cybercriminals and there is nothing stopping them from simply taking the money and not providing anything in return. It has happened to many victims in the past and will continue to happen in the future as crooks are unlikely to feel obligated to help users. Furthermore, as long as victims continue paying the ransom, the ransomware business will continue to thrive.
If you have a backup of your files, you can start recovering them as soon as you remove Hoop ransomware from your computer. If the ransomware is still present when you access your backup, backed-up files would become encrypted as well. Thus, you need to be very careful to fully get rid of the ransomware. If you have not backed up your files, your options are, unfortunately, very limited. There is a free Djvu/STOP ransomware decryptor developed by Emsisoft but it will not work on Djvu versions released after 2019, and that includes Hoop Ransomware. Nonetheless, it’s not impossible that a decryptor will be released sometime in the future. Thus, back up encrypted files and occasionally check NoMoreRansom for a free decryptor.
Ransomware distribution methods
This ransomware uses the standard spread methods, including malicious email attachments, torrents, and malicious ads. In many cases, it’s users’ bad browsing habits that lead to infections. Thus, developing better ones can go a long way towards preventing a ransomware infection.
One of the most common ways ransomware spreads is via malicious email attachments. Malicious actors purchase thousands of email addresses from hacker forums and then use them to launch massive malspam campaigns that carry ransomware. Fortunately for users, the emails with malicious attachments are often fairly obvious. They are full of grammar and spelling mistakes and often make very little sense. The tone of those emails is often meant to scare the user into opening the attachment. For example, the sender may claim to be from some government agency and pressure the user to open the attachment by saying it’s an important document. However, if you look at such scam emails more closely, it’s rather obvious that they’re not real. For instance, they address users with Customer, Member, User, etc., instead of with their names. If users are contacted by government agencies or any reputable company whose services they use, they would always be addressed by name as that’s standard practice. So whenever you receive an unsolicited email with an attachment, pay attention to every detail. It’s also recommended to scan the file with anti-virus software or VirusTotal to check whether it contains malware before opening it.
Another common way ransomware is distributed is via torrents. If you are a torrent user, you are likely already aware that many torrent sites are badly moderated, which allows cyber crooks to easily upload malware disguised as some kind of popular entertainment content. It’s very common for torrents for popular movies, TV shows, video games, and software to contain malware, which is one of the reasons why pirating is discouraged.
Hoop Ransomware removal
Because ransomware is a complex infection, use anti-virus software to delete Hoop Ransomware from your computer. If you try manual Hoop Ransomware removal, you may end up causing even more damage. And once the ransomware is no longer present, you can access your backup to start recovering files. As we mentioned already, be careful to fully remove Hoop Ransomware before accessing backup because otherwise, those files would become encrypted as well.
If you do not have a backup, your only option may be to wait for a free decryptor to become available. While it hasn’t been released at the time of writing, that may change in the future. Back up the files that have been encrypted and check NoMoreRansom or other legitimate decryptor sources every now and then. You should also start backing up your files on a regular basis to avoid file loss in the future.
Site Disclaimer
WiperSoft.com is not sponsored, affiliated, linked to or owned by malware developers or distributors that are referred to in this article. The article does NOT endorse or promote malicious programs. The intention behind it is to present useful information that will help users to detect and eliminate malware from their computer by using WiperSoft and/or the manual removal guide.
The article should only be used for educational purposes. If you follow the instructions provided in the article, you agree to be bound by this disclaimer. We do not guarantee that the article will aid you in completely removing the malware from your PC. Malicious programs are constantly developing, which is why it is not always easy or possible to clean the computer by using only the manual removal guide.